The classic fingerprint-without-card technology is simple and in many cases what serves our customers’ basic needs best. The fingerprint reader solution replaces codes or passwords.
2-factor authentication:
Precise Biometrics also offers products with 2-factor authentication, combining smart card and fingerprint. With this solution the fingerprint is stored on the smart card. Using templates on a card offers vast scalability, higher security and fast matching times. Using the correct access keys can only access the fingerprint data.
3-factor authentication
A product with 3-factor authentication, combines smart card, fingerprint and PIN code.
26 Bit Format: H10301
The 26-bit format is the industry standard format, and is an open format. The sale of this format is not limited to any one company. The range of card numbers available in this format is limited and therefore there is a potential for card numbers to be duplicated. It is important to understand that HID does not insure that card numbers will not be duplicated. HID does not control or restrict the ordering of cards encoded with the standard 26 bit format. Convenience in ordering cards and universal access control panel acceptance are the primary benefits in using the standard 26 bit card format. It consists of 255 possible facility codes. Within each facility code there is a total of 65,535 unique card numbers.
The standard 26 bit Wiegand format is H10301. It is binary encoded data. The format consists of 2 parity bits, 8 bit facility code and 16 bit card number fields. The format is shown below.
PAAAAAAAABBBBBBBBBBBBBBBBP
EXXXXXXXXXXXX
XXXXXXXXXXXXO
where:
P = Parity
O = Odd Parity
A = Facility code, range = 0 to 255 E = Even Parity
B = Card Number, range = 0 to 65,535 X = Parity mask
125 kHz Credentials- HID Proximity
With over 200 million credentials in use around the world, HID proximity cards are recognized as the industry standard for physical access control. Featuring 125 kHz RFID technology HID prox products are robust, affordable, and seamlessly integrate with access control systems. Some cards are:
1391 MicroProx Tag:- HID Proximity Adhesive Tag; 1324 Adhesive Label, Printable label for ProxCard II Clam-shell Card;
1386 ISOProx II Card. ISO-Thin:- Imageable HID Proximity Access Card.
1598 Smart DuoProx II Card:- Multi-Technology Card with Magnetic Stripe, Contact Smart Chip Embeddable.
16-9 ProxCard Plus:- HID Proximity Card with Wiegand Proximity Key Fob.
1326 ProxCard® II Clamshell Card:- Value Priced HID Proximity Card, 1351 ProxPass II Active Tag ,Long Range Proximity Tag for Vehicle Access Control.
13.56 MHz Credentials - iCLASS Contactless
Optimized to make physical access control more powerful,iCLASS 13.56 MHz read/write contactless smart card technology provides versatile interoperability and supports multiple applications such as biometric authentication, cashless vending and PC log on security.
iCLASS smart cards and readers make access control more powerful, more versatile, and most important of all, offers enhanced security through encryption and mutual authentication. At the same time, iCLASS is user-friendly, delivering the convenience, affordability and reliability of proximity technology for which HID is known worldwide.
Some cards are: 200X iCLASS Card:- For Direct Image & Thermal Transfer;
202X iCLASS Prox Card:- 13.56 MHz iCLASS Card with 125 kHz HID Proximity.
213X iCLASS Embeddable Card and iCLASS Prox Embeddable Card, iCLASS Card with or without 125 kHz HID Proximity and an Optional Contact Smart Chip Module.
204X iCLASS Wiegand Combo Card:- 13.56MHz Contactless Smart Card with Wiegand.
2080 iCLASS Clamshell Card:-Value Price 13.56 MHz Contactless Smart Card.
13.56 MHz Credentials - FlexSmart® Series MIFARE®/DESFire®
FlexSmart Series Credential, MIFARE and DESFire, both offerings encompass the industry’s broadest range of open standard contactless smart card products. Manufactured to the highest quality standards, HID MIFARE and DESFire credentials have the memory structure and capacity to store multiple applications on a single credential. When security and performance count most, HID’s FlexSmart MIFARE and DESFIre credentials can be produced with visual security and anti-counterfeiting features such as holograms, ultra-violet fluorescent inks, micro-printing or a custom logo to quickly and easily identify genuine cards.
Some cards are:
1430 MIFARE® ISO Card:- 13.56 MHz MIFARE, ISO Thick, Photo Imageable.
1431 MIFARE® / HID Prox Combo Card:- ISO Thick, Photo Imageable, MIFARE plus HID Prox.
FPMXI MIFARE® / Indala® Prox Combo Card:- 13.56 MHz ISO Thick, Photo Imageable MIFARE plus Indala Prox.
1434 MIFARE® Keyfob:- 13.56 MHz Contactless KeyFob.
1435 MIFARE® 13.56 MHz Adhesive Tag:- Upgrade for Magstripe and Barium Ferrite Cards.
1451 DESFire® / HID Prox Combo Card:- 13.56 MHz ISO Thick, Photo Imageable DESFire plus HID Prox.
1454 DESFire® Keyfob:- 13.56 MHz Contactless Fob
Access Control
Access Control is a mechanism by which a system grants or revokes the right to access some data, or perform some action. Normally, a user must first Login to a system, using some Authentication system. Next, the Access Control mechanism controls what operations the user may or may not make by comparing the User ID to an Access Control database.
Access Control systems include:
• File permissions, such as create, read, edit or delete on a file server.
• Program permissions, such as the right to execute a program on an application server.
• Data rights, such as the right to retrieve or update information in a database.
Access control topology
Access control decisions are made by comparing the credential to an access control list. This lookup can be done by a host or server, by an access control panel, or by a reader. The development of access control systems has seen a steady push of the lookup out from a central host to the edge of the system, or the reader. The predominate topology circa 2009 is hub and spoke with a control panel as the hub and the readers as the spokes. The lookup and control functions are by the control panel. The spokes communicate through a serial connection; usually RS485. Some manufactures are pushing the decision making to the edge by placing a controller at the door. The controllers are IP enabled and connect to a host and database using standard networks.
Access control system components
An access control point, which can be a door, turnstile, parking gate,
elevator, or other physical barrier where granting access can be
electrically controlled. Typically the access point is a door. An
electronic access control door can contain several elements. At its
most basic there is a stand-alone electric lock (EM Lock). The lock is
unlocked by an operator with a switch. To automate this, operator
intervention is replaced by a reader. The reader could be a keypad
where a code is entered, it could be a card reader, or it could be a
biometric reader. Readers do not usually make an access decision but
send a card number to an access control panel that verifies the number
against an access list. To monitor the door position a magnetic door
switch is used. In concept the door switch is not unlike those on
refrigerators or car doors. Generally only entry is controlled and
exit is uncontrolled. In cases where exit is also controlled a second
reader is used on the opposite side of the door. In cases where exit
is not controlled, free exit, a device called a request-to-exit (REX /
Egress Switch ) is used. Request-to-exit devices can be a pushbutton
or a motion detector. When the button is pushed or the motion detector
detects motion at the door, the door alarm is temporarily ignored
while the door is opened. Exiting a door without having to
electrically unlock the door is called mechanical free egress. This is
an important safety feature. In cases where the lock must be
electrically unlocked on exit, the request-to-exit device also unlocks
the door.
Access Area
A specific defined area wherein all access points to the area are
secured by the system, and the access points can be configured and
adjusted to set parameters on occupancy and permission attributes.
Access Credential
A medium that contains encoded information (which is recognized by the
access control system) such as ID cards, key fobs, biometrics, and
smart chips.
Access Level
A logical group of doors paired with a time schedule used to determine
when and where a card is granted access in the system.
ACM (Access Control Model)
A group of objects that when associated together form a point of entry
that is normally associated with a door or elevator.
Acquisition device:
The hardware used to acquire biometric samples.
Active imposter acceptance:
Acceptance of a biometric sample submitted by someone attempting to
gain illegal entry to a biometric system.
ADA (American Disabilities Act)
Indicates that a setting or card designation is compliant with the
American Disabilities Act, which provides specific parameters for
access for personnel with disabilities. Cards with the ADA setting
checked, enable ADA parameters to take effect when the card is badged.
Administrator
Person responsible for adding operators and assigning the specific
privileges to the operators’ profiles, and determining operator
levels.
AFIS:
Automated Fingerprint Identification System (or AFIS) is a system to
automatically match one or many unknown fingerprints against a
database of known prints. This is done for miscellaneous reasons, not
the least of which is because the person has committed a crime. With
greater frequency in recent years, AFIS like systems have been used in
civil identification projects. The intended purpose is to prevent
multiple enrollment in an election, welfare, DMV or similar system.
The FBI manages a fingerprint identification system and database
called IAFIS, which currently holds the fingerprints and criminal
records of over fifty-one million criminal record subjects, and over
1.5 million civil (non-criminal) fingerprint records. US Visit
currently holds a repository of over 50 million persons, primarily in
the form of two-finger records (by 2008, US Visit is transforming to a
system recording FBI-standard tenprint records).
Algorithm
A sequence of instructions that tell a biometric system how to solve a
particular problem. An algorithm will have a finite number of steps
and is typically used by the biometric engine to compute whether a
biometric sample and template are a match.
APB (Anti Pass Back)
Control prohibiting a card from entering an access area more than once
without the system recognizing that the card has first exited the
access area.
Anti-Passback (APB) prevents users from 'tailgating' through
controlled areas by tracking the entry and exit counts. A user can
only exit an area that they have already entered and can only enter an
area that they previously exited. If a user tailgates onto a site, the
exit keypad will deny exit to them because they are not logged into
the area. If a user is onsite and tailgates off of the site, they will
be denied exit next time they try to enter. Anti-Pass back (APB) is a
function that should only be used on High Security sites where users
can be trained on its use.
API
Application Program Interface. A computer code which is a set of
instructions or services used to standardize an application. Any
system compatible with the API can then be added or interchanged by
the application developer.
Alarm Screens
- These are standard window screens that have a special wire woven in
the screening. They are designed to detect someone cutting the screen.
ASIC
Application Specific Integrated Circuit. An integrated circuit
developed for specific applications to improve performance.
Attempt
The submission of a biometric sample to a biometric system for
identification or verification. A biometric system may allow more than
one attempt to identify or verify.
Authentication:
Any systematic method of confirming the identity of an individual.
Some methods are more secure than others. Simple authentication
methods include user name and password, while more secure methods
include token-based one-time passwords. The most secure authentication
methods include layered or "multi-factor biometric procedures. This is
independent of authorization.
Authentication Routine
A cryptographic process used to validate a user, card, terminal, or
message contents. Also known as a handshake, the routine uses
important data to create a code that can be verified in real time or
batch mode.
Authorization Server
The Authorization Server maintains all client license and
sub-controller license info. Also manages concurrent clients.
Automatic ID/Auto ID
An umbrella term for any biometric system or other security technology
that uses automatic means to check identity. This applies to both
one-to-one verification and one-to-many identification.
Audit trail
In computer/network systems: Record of events (protocols, written
documents, and other evidence) which can be used to trace the
activities and usage of a system. Such material is crucial when
tracking down successful attacks/attackers, determining how the
attacks happened, and being able to use this evidence in a court of
law.
American National Standards Institute (ANSI)
Established in 1918, ANSI is a voluntary organization that creates
standards for the computer industry. The FBI commissioned ANSI to
create an image standard for the exchange of fingerprint data between
AFIS systems.
ANSI 378
Interoperability standard for fingerprint templates developed by the
American National Standards Institute (ANSI). The US governmental
requires the use of ANSI 378 templates for Homeland Security Directive
(HSPD-12) and Personal Identity Verification (PIV). The US Federal
requirements for ANSI 378 are designed to ensure that all employees
and contractors are able to use their badges for identification and
access to all government facilities.
Access control system components
An access control point, which can be a door, turnstile, parking gate,
elevator, or other physical barrier where granting access can be
electrically controlled. Typically the access point is a door. An
electronic access control door can contain several elements. At its
most basic there is a stand-alone electric lock (EM Lock). The lock is
unlocked by an operator with a switch. To automate this, operator
intervention is replaced by a reader. The reader could be a keypad
where a code is entered, it could be a card reader, or it could be a
biometric reader. Readers do not usually make an access decision but
send a card number to an access control panel that verifies the number
against an access list. To monitor the door position a magnetic door
switch is used. In concept the door switch is not unlike those on
refrigerators or car doors. Generally only entry is controlled and
exit is uncontrolled. In cases where exit is also controlled a second
reader is used on the opposite side of the door. In cases where exit
is not controlled, free exit, a device called a request-to-exit (REX)
is used. Request-to-exit devices can be a pushbutton or a motion
detector. When the button is pushed or the motion detector detects
motion at the door, the door alarm is temporarily ignored while the
door is opened. Exiting a door without having to electrically unlock
the door is called mechanical free egress. This is an important safety
feature. In cases where the lock must be electrically unlocked on
exit, the request-to-exit device also unlocks the door.
Attendance Management
Attendance management is the act of managing attendance or presence in
a work setting to minimize loss due to employee downtime. Attendance
control has traditionally been approached using time clocks,
timesheets, and time tracking software, but attendance management goes
beyond this to provide a working environment which maximises and
motivates employee attendance.
Bit
A bit or binary digit is the basic unit of information in computing
and telecommunications, it is the amount of information that can be
stored by a digital device or other physical system that can usually
exist in only two distinct states. In information theory, one bit is
typically defined as the uncertainty of a binary random variable that
is 0 or 1. There are several units of information which are defined as
multiples of bits, such as byte (8 bits), kilobit (either 1000 or 210
= 1024 bits), megabyte (either 8000000 or 8×220 = 8388608bits), etc.
Byte
The byte (pronounced /baɪt/) is a unit of digital information in
computing and telecommunications. It is an ordered collection of bits,
in which each bit denotes the binary value of 1 or 0. Historically, a
byte was the number of bits (typically 5, 6, 7, 8, 9, or 16) used to
encode a single character of text in a computer and it is for this
reason the basic addressable element in many computer architectures. B
as the symbol for byte (e.g., MB means megabyte, KB is commonly used
for kilobyte).In certain programming languages. The C and C++
programming languages, for example, define byte as "addressable unit
of data large enough to hold any member of the basic character set of
the execution environment" (clause 3.6 of the C standard). The C
standard requires that the char integral data type is capable of
holding at least 255 different values, and is represented by at least
8 bits (clause 5.2.4.2.1). Various implementations of C and C++ define
a byte as 8, 9, 16, 32, or 36 bits
Bit rate
In telecommunications and computing, bitrate (sometimes written bit
rate, data rate or as a variable R ) is the number of bits that are
conveyed or processed per unit of time.
The bit rate is quantified using the bits per second (bit/s or bps)
unit, often in conjunction with an SI prefix such as kilo- (kbit/s or
kbps), mega- (Mbit/s or Mbps), giga- (Gbit/s or Gbps) or tera- (Tbit/s
or Tbps). Note that, unlike many other computer-related units, 1 kbit/s
is traditionally defined as 1,000 bit/s, not 1,024 bit/s, etc,
32 kbit/s – MW (AM) Audio quality
96 kbit/s – FM Audio quality
128–160 kbit/s – Standard Bitrate Audio quality
224–320 kbit/s – VBR to highest MP3 Audio quality
800 bit/s – minimum necessary for recognizable speech
8 kbit/s – telephone quality
32-500 kbit/s -- lossy audio
256 kbit/s - Digital Audio Broadcasting
400 kbit/s–1,411kbit/s – lossless audio as used in formats such as
Free Lossless Audio Codec, WavPack or Monkey's Audio to compress CD
audio
1,411.2 kbit/s – Linear PCM sound format
5,644.8 kbit/s – DSD
16 kbit/s – videophone quality
1.15 Mbit/s max – VCD quality
3.5 Mbit/s typ - Standard-definition television quality
8 to 15 Mbit/s typ – HDTV quality
24 Mbit/s max - AVCHD
29.4 Mbit/s max – HD DVD
40 Mbit/s max – Blu-ray Disc
Baud
In telecommunications and Access Control electronics, baudis
synonymous to symbols per second or pulses per second. It is the unit
of symbol rate, also known as baud rate or modulation rate; the number
of distinct symbol changes (signaling events) made to the transmission
medium per second in a digitally modulated signal or a line code.
A baud rate of 1 kBd = 1,000 Bd is synonymous to a symbol rate of
1,000 symbols per second. In case of a modem, this corresponds to
1,000 tones per second, and in case of a line code, this corresponds
to 1,000 pulses per second. The symbol duration time is 1/1,000 second
= 1 millisecond.
Baud Rate
In telecommunications and Access Control electronics baud rate is a
technical term associated with modems and other technical devices. It
is also known as symbol rate and modulation rate. The term roughly
means the speed that data is transmitted. It is a derived value based
on the number of symbols transmitted per second. Baud can be
determined by using the following formula: Baud = (Gross Bit Rate /
Number of Bits per Symbol). This can be used to translate baud into a
bit rate using the following formula: Bit Rate = (Bits per Symbol *
Symbol Rate). Baud can be abbreviated using the shortened form “Bd”
when being used for technical purposes. A system using 4800 baud
modems that has 4 bits per symbol will send less data than a system
using 9600 baud modems that also has 4 bits per symbol. So, all other
things being equal, a higher baud rate is generally preferred.
Badge
An identification card usually displaying a cardholder’s photo,
signature or other specific identifying characteristics.
Badging Station
A hardware and software system used to obtain and save personal data
about a cardholder (e.g., photo or signature).
Basic (non-intelligent) Readers
simply read card number or PIN and forward it to a control panel. In
case of biometric identification, such readers output ID number of a
user. Typically Wiegand protocol is used for transmitting data to the
control panel, but other options such as RS-232, RS-485 and Clock/Data
are not uncommon.This is the most popular type of access control
readers. Examples of such readers are RF Tiny by RFLOGICS, ProxPoint
by HID, and P300 by Farpointe Data.
Bar Code
A array of machine readable rectangular bars and spaces arranged in a
specific way to represent letters, numbers, and other human readable
symbols.
Broadband Internet access
Broadband Internet access, often shortened to just broadband, is a
high data rate Internet access—typically contrasted with dial-up
access using a 56k modem.
Dial-up modems are limited to a bit rate of less than 56 kbit/s
(kilobits per second) and require the full use of a telephone
line—whereas broadband technologies supply more than double this rate
and generally without disrupting telephone use.
Although various minimum bandwidths have been used in definitions of
broadband, ranging up from 64 kbit/s up to 2.0 Mbit/s, the 2006 OECD
report is typical by defining broadband as having download data
transfer rates equal to or faster than 256 kbit/s, while the United
States (US) Federal Communications Commission (FCC) as of 2010,
defines "Basic Broadband" as data transmission speeds of at least 4
megabits per second (Mbps), or 4,000,000 bits per second, downstream
(from the Internet to the user’s computer) and 1 Mbps upstream (from
the user’s computer to the Internet). The trend is to raise the
threshold of the broadband definition as the marketplace rolls out
faster services
BioAPI
BioAPI (Biometric Application Programming Interface) is a key part of
the International Standards that support systems that perform
biometric enrollment and verification (or identification). It defines
interfaces between modules that enable software from multiple vendors
to be integrated together to provide a biometrics application within a
system, or between one or more systems using a defined Biometric
Interworking Protocol (BIP)
BioAPI V1.0, developed by the BioAPI consortium, and released in March
2000. Designed to produce a standard biometric API aiding developers
and consumers.
Biometrics
Biometrics(ancient Greek: bios ="life", metron ="measure") refers to
two very different fields of study and application.A machine readable
technology that allows for the unique identification of individuals by
reading biological features (fingerprints, retina scans, Hand Geometry
etc.).
Behavioral Biometric
A biometric that is characterized by a behavioral trait that is
learned and acquired over time, rather than a physical or
physiological characteristic.
Boom barrier
 A
boom barrier is a bar, or pole pivoted in such a way as to allow the
boom to block vehicular access through a controlled point. Typically
the tip of a boom gate rises in a vertical arc to a near vertical
position. Boom gates are often counter-weighted, so the pole is easily
tipped. Boom gates are often paired either end to end, or offset
appropriately to block traffic in both directions. Some boom gates
also have a second arm, which pivots on links that allow the second
arm to hang 300 to 400 mm below the upper arm when it descends into
the horizontal position, in order to increase approach visibility.
A
boom barrier is a bar, or pole pivoted in such a way as to allow the
boom to block vehicular access through a controlled point. Typically
the tip of a boom gate rises in a vertical arc to a near vertical
position. Boom gates are often counter-weighted, so the pole is easily
tipped. Boom gates are often paired either end to end, or offset
appropriately to block traffic in both directions. Some boom gates
also have a second arm, which pivots on links that allow the second
arm to hang 300 to 400 mm below the upper arm when it descends into
the horizontal position, in order to increase approach visibility.
Boom gates are typically found at
level(rail)crossings,drawbridges,parking facilities, checkpoints and
entrances to restricted areas. They are also the usual method for
controlling passage through toll booths.
Some boom gates are automatic and powered, others are manually
operated. Manual gates are sometimes hung in the manner of a normal
gate (i.e. hinged horizontally).
Bifurcation
A branch made by more than one finger image ridge.
Biometric Authentication Mode
The way biometric data (e.g. fingerprints) is used for authentication.
The mode chosen for a biometric installation depends on the specific
needs of a site, where either convenience or security may be
emphasized. BioCert fingerprint devices may use either of two
biometric authentication modes, identification or verification.
Biometric Authorization System
Authorization means whether the user has an authority or permission to
access something. This something could be a computer, secured
location, etc.
A good example of authorization is going to a movie theater to watch a
movie.Before entering the premise, you are asked to show the movie
ticket. If you have the movie ticket, then they let you pass through,
else you are denied. Please note the person who is checking the ticket
does know who you are, he/she will allow you only if you have a valid
ticket. The point is that no identification or verification has taken
place. It is assumed that the person who is carrying the movie ticket
is the person to whom the movie ticket belongs.
Let’s look at another example. Let’s say, you sit at a front desk, and
your boss hands you file with people’s name, and says, “Please let
only these people walk in through the door.” A person walks up to you
and says, “Hi, this John and I need to go through the door”. What will
you do? You will first verify the person’s identity, and then check if
his name is on the list. If you find his name on the list, then it
means that he has the permission to go through the door. If his name
is not on the list, then you will say, “I am sorry, you don’t have the
permission to go through the door.” This is a secured form of
authorization. Please note that in this case verification takes place
before authorization.
Let’s consider fingerprint-based computer login system. A person
wanting to access the computer system will place the finger on the
fingerprint scanner. The biometric system will capture the
fingerprints and compare it with the fingerprints of the people who
have access to the system. If a match is found, then give the person
is given access to the computer system, else the access is denied. In
this example, verification is followed by authorization. Placing the
finger on the fingerprint scanner means verifying that it is the same
person who is asking the access to the system. Authorization happens
when the computer returns a yes or a no response to the user’s request
for accessing the system.
Such systems could be are 1:N or 1:1. If the authorization is done
using only the fingerprints, then the matching will have to be done
with all the fingerprints in the database, hence the system will be of
type 1:N. However, if a person is asked to submit a unique identifier
(such as, user-id) along with the fingerprints, then only one matching
takes place, that is with the fingerprints associated with the unique
identifier. Such a system is of type 1:1.
Biometric Identification System
Identification means you don’t know anything about the person and you
are trying to identify them, e.g., you go to a party, someone comes up
and says, “hi”. What do you do? You look at the person’s face, and try
to recognize them. The same process happens in the biometric
identification solution.
Let’s say, you have pictures of all the users in the database. Now,
someone comes up to you and says “Hi”, what you will do? You will take
a picture of this person and feed it to your biometric system.The
biometric system will compare this picture with all the pictures that
are in database & returns the information of that person, whose
photograph is the closest match. This is also called 1:N matching,
where the biometric system is comparing 1 picture with all the
pictures in the database.
In this example, we have used the face recognition technology to
identify a person, but we can use fingerprint, iris, voice or any
other biometric technology.
Biometric Verification System
Verification means verifying a person’s identity.
When a person walks up to you and says, “Hi, I am Arindam” and shows
you his ID card. You look at the person’s face, look at the picture,
and try to match them. If they match, then it means that the person is
verified, if it doesn’t, then you know that the person is not Arindam
but someone else. The same process happens in the biometric
verification system.
A person walks up to you, and says, “Hi, I am Arindam”. As before, you
will take the picture of Arindam, and feed it to your biometric
system. This time you will inform the system that this person claims
to be “Arindam”. The biometric system will then pull up Arindam’s
file; try to match Arindam’s face with the picture associated with the
file. If the picture matches, then it will return a positive response
indicating that the person is “Arindam”, else, a negative response,
indicating that the person is not Arindam. This is system is also
called 1:1 matching as only one comparison takes place.
Please note that the verification is not based on only photo IDs. You
could also use pass code, userid-password or any information that only
that user and the person who is verifying the identity, will know.
Biometric template
Biometric templates are representations of a fingerprint or other
biometric using series of numbers and letters. Templates are created
using sophisticated algorithms, a mathematical process.
Biometric Match
This is the name given to the the decision that a biometric sample and
a reference template stored in a biometric database comes from the
same human source, based on their high level of similarity.
A biometric match may consist of a score which designates the
degree of similarity between the sample and the reference template.
Typically, a match should never be identical;freshly gathered samples
will inevitably vary somewhat from the reference template, due to
subtle changes over time and errors in the process of feature
extraction.
Some biometric systems may flag an exact match as a potential fraud;
presenting an exact match implies that the reference template database
has been compromised. The sample must score above the predetermined
biometric match threshold.
Biometric System
An automated system capable of capturing a biometric sample from an
end user; extracting biometric data from that sample; comparing the
biometric data with that contained in one or more reference templates;
deciding how well they match; and indicating whether or not an
identification or verification of identity has been achieved.
Biometrics
The automated technique of measuring a physical characteristic or
personal trait of an individual and comparing that characteristic to a
comprehensive database for purposes of identification.
Biometric sample
The identifiable, unprocessed image or recording of a physiological
or behavioral characteristic, acquired during submission, used to
generate biometric templates.
Biometrics Algorithm
A biometrics algorithm is sequence of instructions that tell a
biometric system how to solve a particular problem.
Typically, biometric systems use these sequences of rules to
interpret data that has been abstracted from the original source. For
example, rather than work on fingerprint images directly, biometric
systems take from a particular print a set of features that best
defines differences between individuals.
An algorithm will have a finite number of steps and is typically used
by the biometric engine to compute whether a biometric sample and
template is a match.
Bumping
Sending an alarm to an alternate site or station following a
user-defined time during which the alarm is unacknowledged.
Buffer overflow
Most common cause of current security vulnerabilities. A buffer
overflow occurs when more data is put into a temporary data storage
area (buffer) than the buffer can hold. Because buffers can only hold
a finite amount of data, the extra information can overflow into
adjacent buffers, corrupting or overwriting the data in them.
Programming errors are the one of the most frequent causes of buffer
overflow problems. In attacks which exploit buffer vulnerabilities,
extra data is sent to the buffer with code designed to trigger
specific actions, and which can damage files, change data, or disclose
confidential information. Buffer overflow attacks may have arisen from
poor use of the C programming language.
Cardholder
Anyone who has been given an access credential.
Card Reader
A card reader is anything, usually an electronic device, which reads
'cards'. There is a wide variety of things called cards and hence
there are many things called 'card readers'.
Access control card readers are used in physical security systems to
read a credential that allows access through access control points,
typically a locked door. An access control reader can be a magnetic
stripe reader, a bar code reader, a proximity reader, a smart card
reader, or a biometric reader.
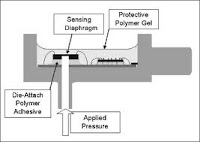
Capacitive Sensors
Capacitive sensors use an array capacitor plates to image the
fingerprint. Skin is conductive enough to provide a capacitive
coupling with an individual capacitive element on the array. Ridges,
being closer to the detector, have a higher capacitance and valleys
have a lower capacitance. Some capacitive sensors apply a small
voltage to the finger to enhance the signal and create better image
contrast.
Capacitive sensors can be sensitive to electrostatic discharge (shock)
but they are insensitive to ambient lighting and are more resist
contamination issues than some optical designs.
Capture
The method of taking a biometric sample from the end user.
Challenge Response
In biometric identification systems, challenge/response is a method
used to confirm the presence of a person by getting some form of
direct response from the individual. The response gathered can be
either voluntary or involuntary.
In a voluntary response, the end user will consciously react to
something that the system presents.
In an involuntary response, the end user's body automatically responds
to a stimulus. A challenge response can be used to protect the system
against attacks.
Classification
A scheme for categorizing fingerprints according to their overall
patterns. Some fingers do not fit into any of the classes, and some
may have attributes of more than one class.
Covert Sampling
"Covert sampling" refers to a method in which biometric samples are
being collected at a location or in a manner that is not known to
bystanders or to test subjects.
One example of a covert sampling environment would be an airport
checkpoint where face images of passengers are captured by
surveillance cameras and are then compared to a watchlist without
their knowledge.
Coding
Image processing software for extracting minutiae features from the
image.
Closed-set Identification
"Closed-set identification" refers to a biometric task in which an
unidentified individual is known to be in the database of biometric
characteristics and the system attempts to determine his/her identity.
Performance is typically measured by the frequency with which the
individual appears in the system’s highest ranked possible IDs.
Comparison
The process of comparing a biometric sample with a previously stored
reference template or templates. See one-to-many and one-to-one.
Channel
The path in which the SSP controller communicates with the host or
driver.
Command
An operator-initiated event that causes a change or action within the
access control system.
Contactless card
Smart cards or memory cards which communicate by a radio signal. The
range is normally up to 10 cm from the reader.
Contactless Credit Cards
Contactless credit cards differ from regular credit cards in the way
the information is read from them by the card reader. A regular credit
card stores its data on a magnetic stripe that must be physically
swiped through a card reader. A contactless credit card, on the other
hand, stores its data on a microchip embedded in the card's plastic.
The microchip is fitted with a radio antenna that is capable of
transmitting the card's data to a card reader without physical
contact. Using radio frequency identification (RFID) technology with
the ISO 14443 standard, a contactless card can transmit data to a
special RFID card reader when the cardholder waves his card within a
few inches of the receiver.
Smart cards or memory cards which communicate by a radio signal. The
range is normally up to 10 cm from the reader.
Central or on line processing
A system where all systems information is stored in a central location
and all go or no-go decisions are made by this unit.
Crossover error rate (CER)
A comparison metric for different biometric devices and technologies;
the error rate at which FAR equals FRR. The lower the CER, the more
accurate and reliable the biometric device.
Controller
The data-gathering panel that makes local access decisions. Includes
the SSP,SSP-C, and SSPE.
Cables
Consider the following points before select the type of cable to be
used.
1. Current Carrying Capacity - The Current Carrying Capacity /
Gauge of a cable is measured as per the American Wire Gauge (AWG)
standard for expressing wire diameter.
2. Shielding - Good shielding provides protection against interference
from external sources(usually copper, aluminium, or other conductive
material), which are trying to get out of the cable and into the
signal in the cable.
3. Core - Single Conductor /Multi Conductor (Core.
Connection range depends upon controller make to make. As the AWG
number gets smaller, the wire diameter gets larger. This reduces
resistance & cable length can be increased. Here Low Resistance means
Higher Current Carrying Capacities.
Central or on line processing
A system where all systems information is stored in a central location
and all go or no-go decisions are made by this unit.
Common Biometric Exchange File Format (CBEFF)
A standard that provides the ability for a system to identify, and
interface with, multiple biometric systems, and to exchange data
between system components.
DNA Identification Technology
Deoxyribonucleic acid (DNA) Biometrics could be the most exact form of
identifying any given individual. Every human being has its own
individual map for every cell made, and this map, or ‘blueprint’ as it
more often is called,can be found in every body cell. Because DNA is
the structure that defines who we are physically and intellectually,
unless an individual is an identical twin, it is not likely that any
other person will have the same exact set of genes.
DNA can be collected from any number of sources: blood, hair, finger
nails, mouth swabs, blood stains, saliva, straws, and any number of
other sources that has been attached to the body at some time.DNA
matching has become a popular use in criminal trials,especially in
proving rape cases.The main problems surrounding DNA biometric is that
it is not a quick process to identify someone by their DNA. The
process is also a very costly one.
DNA Biometrics is not a fool proof method of identification. If
forensic scientists to not conduct a DNA test properly, a person’s
identification code can be skewed. Another problem is matching prior
DNA samples to new samples; this is a bigger problem in DNA
fingerprinting. The information looks like a bar code, and if not
closely inspected an incorrect match could be made .
Download
An “update” action to send saved information to the SSP.
Distributed processing
An access control system where some of the system information is
stored at the individual readers or controllers. This allows the
system to operate when the host is down or not communicating.
Door forced open
A signal indicating that the door was opened without a valid card or
request to exit device. This requires a status switch and some type of
rex device.
Door held open
A signal that indicates that the door was held open longer than it
should have been. This is used to prevent someone from using a card to
enter and then leave the door open for others. This requires a status
switch on the door.
Door Event
Software to show the status of door on a list, to alert administrator
for any activities happen at the door such as normal door open-close,
door ajar, door open time out etc.
Drop bolt/Dead bolt
A dead bolt or dead lock (also deadbolt), is a
locking mechanism distinct from a spring bolt lock because a deadbolt
cannot be moved to the open position except by rotating the lock
cylinder. The more common spring bolt lock uses a spring to hold the
bolt in place, allowing retraction by applying force to the bolt
itself. A deadbolt can therefore make a door more resistant to entry
without the correct key.
A deadbolt is often used to complement a spring-bolt lock on an entry
door to a building.
Data Encryption Standard (DES)
Data Encryption Standard, a block cipher developed by IBM and the U.S.
Government in the 1970s as an official standard.
Demographic Data
Census information about an individual, such as name, address, gender,
race, and year of birth.
Digital Signature
The encryption of a message digest with a private key.
Direct Fingerprint Reader (DFR)
A device capable of scanning finger images directly from an
individual's fingers.
Dual Interface Card
Dual interface cards have contact and contact less interfaces for data
and transmission in both directions.
Electric strike (OR)Electric Door strike (OR) Electric Latch
Release( EDS / ELR)
An electric strike is an access control device used for doors. It
replaces the fixed strike faceplate often used with a latchbar (also
known as a keeper). Like a fixed strike, it normally presents a ramped
surface to the locking latch allowing the door to close and latch just
like a fixed strike would. However, an electric strike's ramped
surface can, upon command, pivot out of the way of the latch allowing
the door to be pushed open (from the outside) without the latch being
retracted (that is, without any operation of the knob) or while exited
the knob or lever can be turned to allow egress from the secured area.
Suitable For: Wooden Door, Metal Door, Fireproof Door. Electric
strikes come in many varieties. They can be 12V or 24V or even higher
voltage and they may take AC or DC current and some even take both.
They may be fail safe or fail secure. A fail safe electric strike
needs power to keep it locked. A fail secure electric strike stays
locked even without power. The most common by far is a fail secure.
Easy egress
A means of exiting where the person wishing to leave simply turns the
doorknob to exit.
EXIT button
A Request to exit button. A device that must be pushed in order to
release the door.
Electronic Benefits Transfer (EBT)
Electronic Benefits Transfer enables automatic benefits distribution.
It is currently implemented in WIC and Food Stamps programs.
Employee Recognition
There are many employee recognition systems available but Biometrics
provides a cheaper alternative to most, very few people lose their
fingers or eyes when compared with those who lose smart-cards or
forget passwords.
End User
A person who interacts with a biometric system to enroll or have
his/her identity checked.
Enrollee
A person who has a biometric reference template on file.
Encryption
Making information unreadable/difficult-to read for unauthorized
persons.
- Micro Size: 300 lbs (1,300 N) holding force**.
- Mini Size: 600 lbs (2,700 N) holding force
- Midi Size: 800 lbs (3,600 N) holding force
- Standard Size: 1,200 lbs (5,300 N) holding force.
For safety purposes, electric locks can be designed to operate in one of two modes:
1. Fail-Safe – to protect people: The lock is released if power cuts off.
2. Fail-Secure – to protect property: The lock remains closed if power cuts off.
An electromagnet lock is normally used in Fail-Safe situations.
Enrolling
The process of collecting biometric data from the individual, which is
later, processed and stored as a template.
Enrollment Time
The time a person must spend to have his/her biometric reference
template successfully created.
Emergency Card
It is used during hazards like fire, in which it is required that all
employees or visitors should be evacuated from the premise safely. On
showing the emergency card, all doors will be opened permanently with
immediate effect, thereby allowing everyone in the premises to exit.
Enrollment Station
A workstation at which an individual's biometrics (fingerprint,
voice-print, etc.) and personal information (name, address, etc.) can
be entered into a bio-identification system.
Extraction
The process of converting a captured biometric sample into biometric
data so that it can be compared to a reference template.
Ear Canal Identification Technology
It is known from prior art that the acoustical properties of the
ear can be used to identify people uniquely. This kind of biometric
feature cannot easily be copied, and can easily be implemented in a
mobile phone for remote identification, thus replacing conventional,
less reliable methods of identification such as' the PIN code. In the
case of acoustic ear canal biometrics, what is of interest is the
topology of the ear canal, which is unique for every human. An
incoming sound signal is reflected and otherwise modified by the ear
canal to give an aurally reflected signal which exits the ear canal.
A sound signal is directed into the ear of a user, and the frequency
response of the ear canal is measured and analyzed to extract a
feature vector unique to this user. However, since the microphone used
to detect the response from the ear canal must also pick up any
surrounding sound signals, such a measurement system is particularly
prone to error owing to background noise. These unwanted background
noise signals can really only be excluded from the measurement
described by, for example, enclosing the microphone and the ear in
headphones of a size large enough to encompass the entire ear. Since
such headphones are generally cumbersome to use and awkward to
transport, they are impractical for frequent use, and unsuited to user
identification for applications such as telephone banking, telephone
brokerage, etc, which a user generally wishes to carry out with a
mobile phone, whether at home or underway.
Feature Extraction
Biometric feature extraction is the process by which key features of
the sample are selected or enhanced. Typically, the process of feature
extraction relies on a set of algorithms; the method varies depending
on the type of biometric identification used.
Here are some examples of biometric feature extraction
A fingerprint feature extraction program will locate, measure and
encode ridge edgings and bifurcations in the print.
A voice recording may filter out particular frequencies and patterns.
A digital picture may pull out particular measurements, like the
relative positions of the ears, forehead, cheekbones and nose.
Iris prints will encode the mapping of furrows and striations in the
iris.
FAR
False Acceptance Rate Also known as FAR. Measures how frequently
unauthorized persons are accepted by the system due to erroneous
matching. Potentially serious. The FAR of BioCert devices is currently
about 0 .001% and is usually improved by educating users on correct
usage of fingerprint recognition devices, especially in high security
environments.
Fingerprint Identification Unit (FIU)
A biometric system capable of capturing, storing and comparing
fingerprint data for the purposes of verifying an individual's
identity.
Fingerprint Template
A description of all the detected minutiae in a fingerprint pattern.
The template contains each minutia's x/y coordinate, slope, and type,
thus summarizing the characteristics of the fingerprint for purposes
of matching the fingerprint against candidates.
Fingerprint Image Enhancement
A critical step in automatic fingerprint matching is to automatically
and reliably extract minutiae from the input fingerprint images.
However, the performance of a minutiae extraction algorithm relies
heavily on the quality of the input fingerprint images. In order to
ensure that the performance of an automatic fingerprint identification
/verification system will be robust with respect to the quality of the
fingerprint images, it is essential to incorporate a fingerprint
enhancement algorithm in the minutiae extraction module. We have
developed a fast fingerprint enhancement algorithm, which can
adaptively improve the clarity of ridge and furrow structures of input
fingerprint images based on the estimated local ridge orientation and
frequency. We have evaluated the performance of the image enhancement
algorithm using the goodness index of the extracted minutiae and the
accuracy of an online fingerprint verification system. Experimental
results show that incorporating the enhancement algorithms improves
both the goodness index and the verification accuracy.
Furrow
The lower parts of the fingerprint.
Format
A proximity card stores numbers. When a card is waved in front of a
reader, those numbers are sent to the access controller. However, the
controller needs to know how the received information is organized.
This is known as the format.
The 26 bit Wiegand open format is the industry standard. Card
manufacturers such as HID, Indala and AWID sell cards with this format
to any dealer. This 26 bit format is recognized by all access
hardware.
Over the years, formats with a higher number of bits (33, 37, 48, and
50) have been added to increase card security.
However, some of the higher bit formats are "proprietary", and usually
carry a higher price tag. One exception is the HID 37 bit propietary
format, priced similarly to a 26 bit card.
Facility code and serial number
Every card has a consecutive serial number programmed, assigned in
your access control software to a card holder. For 26 bit cards, it
can be from 0 to 65,535.
But, what happens if another company has the same card numbers as
yours? They could access your building and viceversa.
To reduce this risk, a second number, know as the facility or site
code is encoded into each card. This number can go from 0 to 255 on a
26 bit format card.
Then, if your company has cards numbered from 1 to 1000, with facility
code 230, they would be programmed as follows:
230 - 00001
230 - 00002
230 - 00003 .......up to 230 - 01000
The other company could have the same serial numbers, but with
facility code 180, and their cards would be:
180 - 00001
180 - 00002
180 - 00003........up to 180 - 01000
To grant access, your system validates the facility code AND the
serial number. It will rejecting the other company's cards, even if
they have the same serial number, because the facility code does not
match.
Lately, some formats have a greater number of bits, and make obsolete
the notion of facility codes, because the card serial number (like the
serial number on currency bills) is never duplicated at the factory.
This also means faster delivery of cards, even for add-ons to existing
sites, right out of stock.
Cards ship with a facility code (if used) and serial number
programmed.
Fail safe
Is a locking device that is unlocked when no power is applied. Also
called Fail-open. In this configuration, applying electrical current
to the strike will cause it to lock. In this configuration, it
operates the same as a magnetic lock would. If there is a power
failure, the door would open merely by being pushed/pulled open. Fail
safe units are always run using DC power. So, is a locking device that
is unlocked when no power is applied.
Fail secure
Is a locking device that is locked when no power is applied. Also
called Fail-locked or non-fail safe. In this configuration, applying
electrical current to the strike will cause it to open. In this
configuration, the strike would remain locked in a power failure, but
typically the knob can still be used to open the door from the inside
for egress from the secure side. These units can be powered by AC
which will cause the unit to "buzz", or DC power which will offer
silent operation, except for a "click" while the unit releases. These
are not normally used for exit doors since they cannot be unlocked
during a power outage.
Factory default settings
These are the settings that originally applied for a device when it
was first delivered from the factory. If it should become necessary to
reset a device to its factory default settings, this will, for many
devices, completely reset any settings that were changed by the user.
Gait Biometrics
Gait Biometrics is based on the way a person walks. It is a behavioral
type of biometrics. It does not get affected by the speed of the
person's walk.

Advantages of Gait Biometrics:
*Can recognize a person at a distance where other biometrics are
obscured.
**Effective where only low image resolution footage is available,as
with CCTV Cameras.
***Non-invasive biometrics.
Disadvantages of Gait Biometrics:
*It will not work if a person as worn an attire, such as a trench
coat, or a footwear, such as flip-flops, that affects a persons
walking style.
**Sometimes walking surface, downhill, uphill, etc could also cause a
problem
Dongle
A dongle is a small piece of hardware that connects to a laptop or
desktop computer for the purpose of copy protection or authentication
of software to be used on that system.
Electrically, dongles mostly appear as two-interface security tokens
with transient data flow that does not interfere with other dongle
functions and a pull communication that reads security data from the
dongle. These are used by some proprietary vendors as a form of copy
protection or digital rights management, because it is generally
harder to replicate a dongle than to copy the software it
authenticates. Without the dongle, the software may run only in a
restricted mode, or not at all. Vendors of software-protection dongles
(and dongle-controlled software) often use terms such as "hardware
key", "hardware token", or "security device" instead of "dongle", but
the term "dongle" is much more common in day-to-day use. Modern
dongles include built-in strong encryption and use fabrication
techniques designed to thwart reverse engineering. Typical dongles
also now contain non-volatile memory — key parts of the software may
actually be stored and executed on the dongle. Thus dongles have
become secure cryptoprocessor that execute inaccessible program
instructions that may be input to the cryptoprocessor only in
encrypted form.
DHCP
In simple terms, DHCP determines if your IP is static or dynamic and
the length of time an IP address is assigned.
Dynamic Host Configuration Protocol is controlled by a DHCP server.
Your router can be a DHCP server...and if you're on a home network, it
most likely serves this purpose.
I know this might be confusing because the word dynamic is in the
term, but just because you have DHCP enabled on your computer doesn't
mean you can't be assigned a static IP. DHCP enabled on your computer
simply means you're letting a DHCP server assign its IP. Having it
enabled DOES NOT mean it's a DHCP server.
A true DHCP server (not your Linksys router) gives the LAN Admin a ton
of control with IP assigning.
Ever print to a network printer? Ever wonder how that printer keeps
its network assignment? Each network device has a MAC address. You can
assign a static IP at the server to a specific MAC address. This
allows the network printer to always get the same IP even after it
reboots and without assigning the IP at the printer. If you print the
network configuration at the printer, it will probably tell you that
DHCP is enabled and no static IP is assigned. That's because the IP
assignment is handled at the server.
Your ISP has a DHCP server. They can assign IPs by modem MAC
addresses. When your modem comes online, it communicates to the
network indicating it is looking for an IP address. The DHCP server
listens to this communication and starts talking to the modem. The
modem then transmits its MAC address to the DHCP server. At that
point, either an IP has been reserved for the modem or one is assigned
at that time. Hence cloning your MAC address to get a new IP from your
ISP.
Routers and DHCP - Under the General Setup or LAN Setup tab in your
router, you'll see a settings option for DHCP. You can control how
many IPs are assigned or to enable/disable the DHCP server portion of
the router. If you disable it, you'll have to statically assign IPs to
each computer, or have a DHCP server or your network. This goes for
wired and wireless. Any connection on your network has an IP address.
Glass break station
A device mounted near the exit door that can be used to release the
door in the event of an emergency.
Global Anti-Passback
Allows the server to assign any number of readers to the Anti-Passback
function. The server must be online and communicating to the readers
for this to work.
Group
A logical set of common data objects such as cardholders or hardware
points.
GSA APL
In order to eliminate the need for every agency to test and certify
products to implement into HSPD-12, The General Services
Administration (GSA) was asked to create an Approved Products List
(APL). The GSA APL will serve as the buying guide for all of the US
Federal Government Agencies. As agencies begin to implement their
HSPD-12 and PIV solutions they will use the GSA APL to provide
assurance that the products they are purchasing meet guidelines and
technical specifications.
Hand Geometry
Measurement of the layout of the physical characteristics of the hand.
A lesser used biometric technology.
Advantages of Hand Geometry Biometrics:
* Simple, relatively easy to use and inexpensive.
* Hand geometry data is easier to collect, unlike the fingerprints
where a good frictional skin is required by imaging systems, and
retinal data where special lighting is required.
* Environmental factors, such as, dry weather that causes the drying
of the skin is not an issue.
* Usually considered less intrusive than fingerprints, retinal, etc.
Disadvantages of Hand Geometry Biometrics:
* The hand geometry is not unique and cannot be used in identification
systems
* Not ideal for growing children.
* Jewelry (rings, etc), limited dexterity (arthritis, etc) etc may
pose a challenge in extracting the hand geometry information.
* The data size of hand geometry biometrics is large and is not ideal
for using it in embedded systems.
HSPD-12
Abbreviation for US Federal government's Homeland Security
Presidential Directive, which is a set of requirements for government
agencies to improve their security infrastructure.
HTML (Hypertext Markup Language)
HTML is the set of "markup" symbols or codes inserted in a file
intended for display in web browser. The markup tells the browser how
to display the page's words and images for the user.
HTTP (Hypertext Transfer Protocol)
HTTP is the set of rules for exchanging files (text, graphic images,
sound, video, and other multimedia files) on the web. The HTTP
protocol runs on top of the TCP/IP suite of protocols.
HTTPS (Hypertext Transfer Protocol over SSL)
HTTPS is a web protocol used by browsers and web servers to encrypt
and decrypt user page requests and the pages returned by the server.
The encrypted exchange of information is governed by the use of an
HTTPS certificate (issued by a Certificate Authority), which
guarantees the authenticity of the server.
HID Proprietary 37 Bit Format: H10302
In an effort to provide an open format to the industry, while at the
same time provide assurance that the numbers are unique and will not
be duplicated, the 37 bit format was developed. Under this format, HID
controls the issuing of card numbers and does not duplicate the
numbers.
The 37-bit format can be used to program a wide range of unique card
numbers. Although it is available to all customers, not all access
control systems can handle such a large data length format. In
addition, many systems are unable to handle a format that does not
have a facility code. Just like the 26 bit format, the 37 bit format
can be sold to any customer. Although it is available to all
customers, HID controls the numbers to be generated for each order.
Confirm that the system that the cards are to be utilized on is
capable of using a 37-bit number with no facility code.
HID 1326 ProxCard II (26-bit)
The most affordable card from HID and the long-standing industry
choice for proximity access control. The HID ProxCard II card is
approximately the size of a standard credit card and is thin and
flexible enough to be carried in a wallet or on a strap clip. Print to
an adhesive backed PVC card and attach it to the HID ProxCard II in
order to combine your identification card with your proximity card.
HID ProxCard II Key Features
Offers universal compatibility with all HID proximity readers.
Provides durable packaging and consistent read range.
Provides an external number for easy identification and control.
Supports formats up to 85 bits, with over 137 billion codes.
Custom pre-printed artwork available.
A PVC overlay allows for on-site photo ID using most direct image
printers.
Thin enough to carry in a wallet or purse.
Create Photo ID card with model 1324 Printable Adhesive Label
Specifications
Typical Maximum* Read Range for HID ProxCard II
ProxPoint® Plus reader-up to 3" (7.5 cm)
MiniProx® reader-up to 5.5" (14 cm)
ThinLine II® reader-up to 5.5" (14 cm)
ProxPro® reader-up to 8" (20 cm)
ProxPro® II reader-up to 9"(22.9 cm)
Prox80™-up to 5.5" (14 cm)
MaxiProx® reader-up to 24" (60 cm)
*Dependent on local installation conditions.
HID 1336 DuoProx II Card (26-bit)
This card provides a solution for companies desiring to use one card
incorporating proximity, magnetic stripe and photo identification
technologies for multiple applications.
HID DuoProx II multiple technology proximity card offers proximity,
magnetic stripe and photo identification technologies on a single
access control card. HID DuoProx II card is ISO 7810 compliant, with a
nominal thickness of .030". It features a graphics quality surface
optimized for Photo ID printing.
The card is available in standard PVC construction, or a composite
polyester/PVC construction for more demanding high wear and tear
environments( 2.125" x 3.370" x 0.030" ± 0.003" (5.4 x 8.6 x 0.076 ±
0.0076 cm)). For Like all HID ISO cards, the HID DuoProx II card can
be produced with visual security and anti-counterfeiting features such
as holograms, ultra-violet fluorescent inks, micro-printing, or a
custom logo to quickly and easily identify genuine cards.
Specifications
Typical Maximum* Read Range
ProxPoint® Plus reader-up to 2.5" (6.35 cm)
MiniProx® reader-up to 5" (12.7 cm)
ThinLine II® reader-up to 5" (12.7 cm)
ProxPro® reader-up to 7" (17.8 cm)
ProxPro® II reader-up to 8" (20 cm)
Prox80TM Card reader-up to 5" (12.7 cm)
MaxiProx® reader-up to 20" (50.8 cm)
EntryProx reader-up to 2.5" (6.35 cm)
pcProxTM Desktop reader-up to 2.5" (6.35 cm)
*Dependent on local installation conditions.
HID Smart DuoProx II Cards
A longer read range and is able to have a contact smart chip.
Functions just like the DuoProx II cards.
HID 1391 MicroProx Tag (26-bit)
Provides the convenience of HID's proximity technology in a small
disk-shaped( 1.285" / 3.264 cm) transponder. Simply attach the
adhesive-backed Tag to any nonmetallic card or device, and you
instantly have a proximity card!
With the HID MicroProx Tag you can upgrade from magnetic stripe or
barium ferrite technologies by simply adhering the Tag to your
existing access card. Easily and cost-effectively turn a plastic ID
badge or contact smartchip card into a proximity credential!
The Tag can be programmed in any HID proximity format, and is
compatible with all HID proximity readers. Add proximity access
control capability to users' cell phones, PDAs and other similar
nonmetallic devices. Experience the convenience of proximity without
the expense of rebadging!The Tag is RF-programmable for ease of
encoding with HID's ProxProgrammer.
Specifications
Typical Maximum* Read Range
ProxPoint™ reader up to 1.0" (2.5cm)
MiniProx™ reader-up to 2" (5cm)
ThinLine II® reader-up to 1.5" (3.7cm)
ProxPro® reader-up to 3" (7.5cm)
MaxiProx® reader-up to 4.5" (11.4cm)
*Dependent on local installation conditions.
HID 1386 ISOProx II Card (26-bit)
One of the most popular cards available from HID, the ISOProx II
allows you to print identification information on the same card that
you use for access control, eliminating the need to have two cards for
your employees.
The HID ISOProx II Card offers proximity technology with photo
identification capability on a single card. It is ISO 7810 compliant,
with a nominal thickness of .030" (2.125" x 3.370" x 0.030" ± 0.003"
(5.4 x 8.6 x 0.076 ± 0.0076 cm)). The card features a graphics quality
surface optimized for Photo ID printing, and is available in standard
PVC construction, or a composite polyester/PVC construction for more
demanding high wear and tear environments. Like all HID ISO cards, the
HID ISOProx II card can be produced with visual security and
anti-counterfeiting features such as holograms, ultra-violet
fluorescent inks, micro-printing, or a custom logo to quickly and
easily identify genuine cards.
Specifications
Typical Maximum* Read Range
ProxPoint® Plus reader-up to 2.5" (6.25 cm)
MiniProx® reader-up to 5" (12.5 cm)
ThinLine II® reader-up to 5" (12.5 cm)
ProxPro® reader-up to 7" (17.5 cm)
ProxPro® II reader-up to 8" (20 cm)
Prox80™-up to 5" (12.7 cm)
MaxiProx® reader-up to 20" (50 cm)
*Dependent on local installation conditions.
HID Smart ISOProx II Cards
Have a longer read range and are able to have a contact smart chip.
Functions just like the ISOProx II cards.RF-programmable, 125 kHz,
customer-specified ID numbers,locations marked for horizontal and
vertical slot punch.
HID 1346 ProxKey II (26-bit)
is a proximity keyfob offering HID proximity technology in a
convenient, pocket size device(1.90" x 0.90" x 0.35" (4.83 x 2.29 x
0.89 cm)). It easily attaches to a key ring, badge clip or lanyard.
The HID ProxKey II is built to withstand harsh operating environments
or handling. The HID ProxKey II is suited for use in access control
applications where a Photo ID is not required.
HID ProxKey II Keyfobs Features
1.Small enough to fit on a key ring.
2.Universal compatibility with HID proximity readers.
3.Offers universal compatibility with all HID proximity readers.
4.Provides an external number for easy identification and control Can
be placed on a key ring for convenient entry.
5.Supports formats up to 85 bits, with over 137 billion codes.
6.Using HID's ProxProgrammer, card vendors can ship proximity keyfobs,
custom programmed to their customers' requirements, from their own
inventory.
Specifications
Typical Maximum* Read Range
ProxPoint® Plus reader-up to 1.5" (3.7 cm)
MiniProx™- reader-up to 2" (5 cm)
ThinLine II® reader-up to 2" (5 cm)
ProxPro® reader-up to 3" (7.5 cm)
ProxPro®II reader-up to 4" (10.2 cm)
Prox80™-up to 2" (5.1 cm)
MaxiProx® reader-up to 12" (28 cm)
*Dependent on local installation conditions.
HID ProxPass II Active Tags
HID ProxPass tags are made distinctively for vehicle access control.
The HID ProxPass tags make it a lot easier and convenient for fleet
management and parking applications to function(Up to Up to 6 (1.8
m)). The ProxPass tag(9.25cm x 6.75cm x .76cm) can easily be
integrated into a new or existing HID proximity application. Any HID
format can be encoded onto the HID tag. Two to five year battery life,
depending on usage. Compatible with MaxiProx reader and all HID card
formats.
Host
Generally, it is the machine on which the driver resides. Sometimes
refers to a given client machine, e.g. in reference to a host-based
macro.
HID Proprietary 37 Bit Format with Facility Code: H10304
The 37-bit format with facility code differs from the 37-bit format
only in that it also contains a facility code. Just like the 37 bit
without facility code, this format provides the customer with an open
format in which card numbers will not be duplicated, because HID
tracks the manufacture of cards to prevent duplication.
This 37-bit format has 65,535 facility codes available and over
500,000 card numbers within each facility code. Just like the 37-bit
format without facility code, many systems are not capable of handling
a format as large as 37 bits. In addition, many systems are not
capable of handling a facility code as large as 65,535. The 37 bit
format with facility code is ideal for dealers who would like to have
their own format. This allows them to have the security of no
duplication of cards, while at the same time they are not dependent on
any system supplier for a format. This format is reserved for those
customers with a requirement for a large population of cards.
Host Settings
The settings which determine the behavior of the application at the
host or workstation.
HID Long Format Card Programming
HID Long Format Card Programming allows up to 84 bits of user data to
be encoded on a card and transmitted by a reader to the OEM access
control panel or other host controller.
Applications
Long Format allows HID compatibility with longer Wiegand formats sold
in Europe, allows emulation of existing Clock and Data (magstripe)
formats and allows new OEM formats to be created with longer
bitstreams for more security.
Although identified by the reader hardware interface typically used,
any available hardware interface (Wiegand, Clock and Data or Serial)
can be used with any data structure type.
HID Corporate 1000 Program
The Corporate 1000 Program allows HID to provide end-user customers
with a 35-bit card format that is developed specifically for each
individual end-user customer. Within this program,HID can provide the
enduser with just over 1,000,000 individual card numbers within the
assigned format. Card numbers are tracked in the manufacturing process
to ensure that card numbers are not duplicated.
Benefits of the Corporate 1000 Program
* Security of the card and associated data is increased due to the
customized 35-bit format that is proprietary to each individual
end-user.
* HID tracks card number sequences to prevent card number duplication;
the end-user is guaranteed that the card can be used on standard HID
proximity card readers throughout the world. Individual employees can
carry just one card to gain access to any facility in which they have
been authorized. In addition, the end-user may order cards from
multiple sources (as designated by the end-user) and be guaranteed
that card number duplication will not occur.
* Due to the size of the available card population, the end-user is
assured that cards in the desired format will be available for years
to come.
* The end-user is free to choose the access control hardware/software
platform that best meets the needs of individual sites, while insuring
that the same HID reader and card can be used. This provides the
end-user with maximum flexibility in choosing the access control
system and integrator/dealer that best meets their requirements. The
common component is the HID reader and card.
* The end-user has the flexibility to choose the vendor(s) that they
wish to purchase cards from at any time. The end-user may choose to
have one source of supply or many.
Human Biometric Characteristics
Biometric characteristics can be divided in two main classes, as
represented in figure on the right:
• physiological are related to the shape of the body. The oldest
traits, that have been used for more than 100 years, are fingerprints.
Other examples are face recognition, hand geometry and iris
recognition. Visit: www.arindamcctvaccesscontrol.blogspot.com
• behavioral are related to the behavior of a person. The first
characteristic to be used, still widely used today, is the signature.
More modern approaches are the study of keystroke dynamics and of
voice. Visit: www.arindamcctvaccesscontrol.blogspot.com
Strictly speaking, voice is also a physiological trait because every
person has a different pitch, but voice recognition is mainly based on
the study of the way a person speaks, commonly classified as
behavioral.
Other biometric strategies are being developed such as those based on
gait (way of walking), retina, hand veins, ear canal, facial
thermogram, DNA, odor and scent and palm prints.
Infrared cards
Infrared cards contain a series of bar codes, similar to standard bar
code cards, that are only visible when exposed to special infrared
light. When the card is exposed to the special light, the bars cast a
shadow behind the card which is then read by the reader. They are
relatively low in cost, very reliable, not easily duplicated, and
offer a good level of security but can be difficult to laminate for
use as an ID card.
Identification Algorithm
The algorithm used for making a one-to-many search for user identity.
Identification Algorithm
The algorithm used for making a one-to-many search for user identity.
An input fingerprint is first matched at a coarse level to one of the
pre-specified types and then, at a finer level, it is compared to the
subset of the database containing that type of fingerprints only. We
have developed an algorithm to classify fingerprints into five
classes, namely, whorl, right loop, left loop, arch, and tented arch.
The algorithm separates the number of ridges present in four
directions (0 degree, 45 degree, 90 degree, and 135 degree) by
filtering the central part of a fingerprint with a bank of Gabor
filters. This information is quantized to generate a FingerCode which
is used for classification. Our classification is based on a two-stage
classifier which uses a K-nearest neighbor classifier in the first
stage and a set of neural networks in the second stage. The classifier
is tested on 4,000 images in the NIST-4 database. For the five-class
problem, classification accuracy of 90% is achieved. For the
four-class problem (arch and tented arch combined into one class), we
are able to achieve a classification accuracy of 94.8%. By
incorporating a reject option, the classification accuracy can be
increased to 96% for the five-class classification and to 97.8% for
the four-class classification when 30.8% of the images are rejected.
ISO
ISO(International Organization for Standardization)is the world's
largest developer and publisher of International Standards.
ISO is a network of the national standards institutes of 163
countries, one member per country, with a Central Secretariat in
Geneva, Switzerland, that coordinates the system.
ISO is a non-governmental organization that forms a bridge between the
public and private sectors. On the one hand, many of its member
institutes are part of the governmental structure of their countries,
or are mandated by their government. On the other hand, other members
have their roots uniquely in the private sector, having been set up by
national partnerships of industry associations.
Therefore, ISO enables a consensus to be reached on solutions that
meet both the requirements of business and the broader needs of
society.
ISO 7816-1 Smart Card Standard
This part describes the physical charcteristics of integrated circuit
cards. It includes accomodation of exposure limits for a number of
electromagnetic phenomena such as X-rays, UV light, elacromagnetic
fields, static electrical fields, and ambient temperature of the card.
ISO7816-1 defines the characteristics of a card when it is bent or
flexed. This is to make sure that plastic cards with embedded chips
are manufactured in a way that guarantees flawless operation over the
expected life time of a card. Connections beween the surface
connectors and the I/O pins of the embedded silicon die must be
maintaned and withstand mechanical stress. Bending and flexing
procedures are standardised in ISO 7816.
ISO 7816-2 Smart Card Standard
ISO 7816 part 2 defines the dimensions and location of the contacts.
This part includes standards about number, function and position of
the electrical contacts.
The integrated circuit card (ICC) has 8 electrical contacts. They are
referred to as C1 through C8. However, not all 8 contacts are
electrically connected to the embedded microprocessor chip and
therefore remain unused.
The following table contains the contact definition according to
ISO7816-2:
C1-- Vcc --Power connection through which operating power is supplied
to the microprocessor chip in the card
C2 --RST =Reset line through which the IFD can signal to the smart
card's microprocessor chip to initiate its reset sequence of
instructions
C3 CLK Clock signal line t hrough which a clock signal can be provided
to the microprocessor chip. This line controls the operation speed and
provides a common framework for data communication between the IFD and
the ICC
C4-- RFU Reserved for future use
C5- GND Ground line providing common electrical ground between the
IFD and the ICC
C6-- Vpp Programming power connection used to program EEPROM of first
generation ICCs.
C7-- I/O Input/output line that provides a half-duplex communication
channel between the reader and the smart card
C8-- RFU Reserved for future use
Iris Recognition
Iris recognition is a method of biometric authentication that uses
pattern recognition techniques based on high-resolution images of the
irides of an individual's eyes. Not to be confused with another less
prevalent ocular-based technology, retina scanning, iris recognition
uses camera technology, and subtle IR illumination to reduce specular
reflection from the convex cornea to create images of the detail-rich,
intricate structures of the iris. These unique structures converted
into digital templates, provide mathematical representations of the
iris that yield unambiguous positive identification of an individual.
Iris recognition efficacy is rarely impeded by glasses or contact
lenses. Iris technology has the smallest outlier (those who cannot
use/enroll) group of all biometric technologies. The only biometric
authentication technology designed for use in a one-to many search
environment, a key advantage of iris recognition is its stability, or
template longevity as, barring trauma, a single enrollment can last a
lifetime.
Info-Ready Reporting
A software development architecture that presents relevant system data
directly within the application rather than having to run multiple
external reports.No Power DNA allows operators to filter system events
through simple drag and drop function as well as making common
reports, such as "who has access", available from the right click
context menu.
Image Database
The database that contains all fingerprint templates in the system.
The image database can contain images of the fingerprints, as well as
photograph and signature images.
IP controllers
Controllers are connected to a host PC via Ethernet LAN or WAN. IP
access controller is an electronic security device designed to
identify users and control entry to or exit from protected areas. A
typical IP access controller supports 2 or 4 basic access control
readers. It may have an internal web server and support configuration
via a browser or via software installed on a host PC.
The main features that distinguish IP controllers from older
generation of serial controllers are: 1. IP controllers connect
directly to LAN/WAN and have all the inputs and outputs necessary for
controlling readers, monitoring door inputs and controlling locks. 2.
IP controllers have an on-board network interface and does not require
the use of a terminal server.
Advantages:
• An existing network infrastructure is fully utilized, there is no
need to install new communication lines.
• There are no limitations regarding the number of controllers (32 per
line in case of RS-485).
• Special RS-485 installation, termination, grounding and
troubleshooting knowledge is not required.
• Communication with controllers may be done at the full network
speed, which is important if transferring a lot of data (databases
with thousands of users, possibly including biometric records).
• In case of an alarm controllers may initiate connection to the host
PC. This ability is important in large systems because it allows to
reduce network traffic caused by unnecessary polling.
• Simplifies installation of systems consisting of multiple sites
separated by large distances. Basic Internet link is sufficient to
establish connections to remote locations.
• Wide selection of standard network equipment is available to provide
connectivity in different situations (fiber, wireless, VPN, dual path,
PoE).
Disadvantages:
• The system becomes susceptible to network related problems, such as
delays in case of heavy traffic and network equipment failures.
• Access controllers and workstations may become accessible to hackers
if the network of the organization is not well protected. This threat
may be eliminated by physically separating the access control network
from the network of the organization. Also it should be noted that
most IP controllers utilize either Linux platform or proprietary
operating systems, which makes them more difficult to hack. Industry
standard data encryption is also used.
• Maximum distance from a hub or a switch to the controller is 100
meters (330 ft).
• Operation of the system is dependent on the host PC. In case the
host PC fails, events from controllers are not retrieved and functions
that required interaction between controllers (i.e. anti-passback)
stop working. Some controllers, however, have peer-to-peer
communication option in order to reduce dependency on the host PC.
IP Reader
Readers are connected to a host PC via Ethernet LAN or WAN. IP reader
is an electronic security device designed to identify users and
control entry to or exit from protected areas.
An IP reader has two features that distinguish it from other access
control readers:
1. Unlike basic readers, IP readers do not require control panels and
operate independently. A basic reader simply sends card numbers to a
panel and does not control an electric lock, door contact or exit
button. If the control panel fails, the basic reader stops working. An
IP reader has inputs for monitoring a door contact, exit button and a
relay for controlling an electric lock. It also has internal memory
for storing the database of users, configuration parameters and
recording events. Such readers are sometimes referred to as
"intelligent readers" or "readers with built-in controllers".
2. IP readers have an on-board network interface (10/100BaseT Ethernet
or Wi-Fi).
The first IP reader was introduced in 1999 by Isonas Security Systems
Inc.
Advantages:
• Most IP readers are PoE capable. This feature makes it very easy to
provide battery backed power to the entire system, including the locks
and various types of detectors (if used).
• IP readers eliminate the need for controller enclosures.
• There is no wasted capacity when using IP readers (i.e. a 4-door
controller would have 25% unused capacity if it was controlling only 3
doors).
• IP reader systems scale easily: there is no need to install new main
or sub-controllers.
• Failure of one IP reader does not affect any other readers in the
system.
Disadvantages:
• In order to be used in high-security areas IP readers require
special input/output modules to eliminate the possibility of intrusion
by accessing lock and/or exit button wiring. Not all IP reader
manufacturers have such modules available.
• Being more sophisticated than basic readers IP readers are also more
expensive and sensitive, therefore they should not be installed
outdoors in areas with harsh weather conditions or high possibility of
vandalism.
• The variety of IP readers in terms of identification technologies
and read range is much lower than that of the basic readers.
Internet service provider(ISP)
An Internet service provider (ISP), also sometimes referred to as an
Internet access provider (IAP), is a company that offers its customers
access to the Internet. The ISP connects to its customers using a data
transmission technology appropriate for delivering Internet Protocol
Paradigm, such as dial-up, DSL, cable modem, wireless or dedicated
high-speed interconnects.
ISPs may provide Internet e-mail accounts to users which allow them to
communicate with one another by sending and receiving electronic
messages through their ISP's servers. ISPs may provide services such
as remotely storing data files on behalf of their customers, as well
as other services unique to each particular ISP.
Key
A string of bits used widely in cryptography, allowing people to
encrypt and decrypt data; a key can be used to perform other
mathematical operations as well.
Keypads
Keypads use a numeric pad, similar to that of a telephone. The user
simply presses his code into the keypad and the system reads the
numbers. This system does not require the user to carry any special
card or token but can less secure since unless the user is very
careful someone may see which numbers are being pressed. Certain
keypads overcome this drawback by scrambling the number layout each
time the keypad is used. Keypads can be use either by themselves or
for high security in conjunction with some card reader technology. In
this manner the user must both present a card and enter a code before
access is granted.
Key Management
The various processes that deal with the creation, distribution,
authentication, and storage of keys.
Keystroke Dynamics Identification Technology
The behavioral biometric of Keystroke Dynamics uses the manner and
rhythm in which an individual types characters on a keyboard or
keypad. The keystroke rhythms of a user are measured to develop a
unique biometric template of the users typing pattern for future
authentication. Raw measurements available from most every keyboard
can be recorded to determine Dwell time (the time a key pressed) and
Flight time (the time between “key down” and the next “key down” and
the time between “key up” and the next “key up”). The recorded
keystroke timing data is then processed through a unique neural
algorithm, which determines a primary pattern for future comparison.
Data needed to analyze keystroke dynamics is obtained by keystroke
logging. Normally, all that is retained when logging a typing session
is the sequence of characters corresponding to the order in which keys
were pressed and timing information is discarded. When reading email,
the receiver cannot tell from reading the phrase "I saw 3 zebras!"
whether:
•that was typed rapidly or slowly
•the sender used the left shift key, the right shift key, or the
caps-lock key to make the "i" turn into a capitalized letter "I"
•the letters were all typed at the same pace, or if there was a long
pause before the letter "z" or the numeral "3" while you were looking
for that letter
•the sender typed any letters wrong initially and then went back and
corrected them, or if he got them right the first time
Landscape
Horizontal orientation of pages, screen displays or badges.
Latent Fingerprint
Latent fingerprints are "left over" fragments usually caused by the
build-up of oily residues on the optic sensor window after repeated
use. The technique used by BioCert devices to defeat "faked"
fingerprints also prevents latent fingerprints from being incorrectly
validated by the system.
Logical Access Control
Logical access refers to the collection of policies, procedures,
organizational structure and electronic access controls designed to
restrict access to computer software and data files.
Logical access encompasses a number of PC- and network-related
applications including secure authentication and/or log-in to the PC
or network, secure email, data encryption, file / folder encryption,
single sign-on and remote VPN access. By collaborating with IT
industry leaders, HID Global has complemented its physical access
control offerings with an extensive portfolio of logical access
offerings enabling a wide range of logical/physical convergence
solutions.
In addition to having HID technology seamlessly integrated into the
new Dell® Latitude™ E-Family of laptops, the company’s portfolio of
logical access products, solutions and capabilities extends the
company’s strategy of providing solutions for the delivery of secure
identity.
Logo
A graphic symbol used to represent a company or organization.
Live Biometric Capture
A "live biometric capture" refers to a device that obtains biometric
information immediately, typically in a digital format, ready for
comparison to a database.
Here are some examples of live biometric capture:
• A fingerprint capture device that electronically captures
fingerprint images using a sensor (rather than scanning ink-based
fingerprint images from a card, or attempting to scan images lifted
from a surface).
• An iris or retinal scanner that immediately provides appropriate
information for database comparison.
• A digital photograph of the person's face.
Liveness Detection
"Liveness detection" is a biometric capture technique used to ensure
that the biometric sample submitted is from an end user. A liveness
detection method can help protect the system against some types of
spoofing attacks.
MAC address
A MAC address is a physical hardware address assigned to each device
that has the capability of connecting to a network. The internet is
nothing more than a large network. The MAC address is something that
is assigned in the chip on the device and is not something the user
can change.
MAC Cloning
MAC cloning can only be done at your router providing it has those
capabilities. Most ISPs assign their IPs based on the MAC address in
your equipment. If the MAC address of your router is 00-11-22-33-44-55
and you connect to your ISP, the DHCP server records your MAC and
assigns an IP. If you disconnect from the ISP, you lose your IP
address. The next time you connect, the DHCP server sees your MAC,
looks to see if it has assigned an IP address to you before. If it has
and the lease time has not expired, it will most likely give you the
same IP address you had before disconnecting. Why clone a MAC address?
New MAC address most likely equals new IP. How to clone your MAC and
if your router has this feature is dependent on the router itself.
You’ll need to find the instructions on the manufacturer’s website.
Machine Readable
A code or characters that can be read by machines.
Magnetic lock
 A
magnetic lock is a simple locking device that consists of an
electromagnet and armature plate. By attaching the electromagnet to
the door frame and the armature plate to the door, a current passing
through the electromagnet attracts the armature plate holding the door
shut. Unlike an electric strike a magnetic lock has no interconnecting
parts and is therefore not suitable for high security applications
because it is possible to bypass the lock by disrupting the power
supply. Nevertheless, the strength of today's magnetic locks compares
well with that of conventional door locks and they cost less than
conventional light bulbs to operate. Power supplies incorporating a
trickle-charged lead-acid battery pack can be used to retain security
for short-term power outages. All magnetic locks(300LBS, 600LBS,
1200LBS ETC) will work only with DC current, usually 12 to 24 volts.
Never connect a magnetic lock to AC current of any voltage.
A
magnetic lock is a simple locking device that consists of an
electromagnet and armature plate. By attaching the electromagnet to
the door frame and the armature plate to the door, a current passing
through the electromagnet attracts the armature plate holding the door
shut. Unlike an electric strike a magnetic lock has no interconnecting
parts and is therefore not suitable for high security applications
because it is possible to bypass the lock by disrupting the power
supply. Nevertheless, the strength of today's magnetic locks compares
well with that of conventional door locks and they cost less than
conventional light bulbs to operate. Power supplies incorporating a
trickle-charged lead-acid battery pack can be used to retain security
for short-term power outages. All magnetic locks(300LBS, 600LBS,
1200LBS ETC) will work only with DC current, usually 12 to 24 volts.
Never connect a magnetic lock to AC current of any voltage.
The magnetic lock should always be installed on the inside (secure
side) of the door. Installation is as simple as installing on the
header of the door frame for out-swinging doors or using a Z-bracket
for in-swinging doors. It is important to make sure the armature plate
and the electromagnet align as closely as possible to ensure efficient
operation. Magnetic locks are almost always part of a complete
electronic security system. Such a system may simply consist of an
attached keycard reader or may be more complex involving connection to
a central computer that monitors the building's security. Whatever the
choice of locking system, fire safety is an important consideration
Magnetic Stripe
Magnetic material, usually applied as a stripe on a card, used to
encode cardholder information.
Magnetic stripe cards
Magnetic stripe cards use the same technology that is employed in
credit cards, and are probably the most common type of card in use.
There are two types of magnetic cards, low-coercivity and high-coercivity.
The high-coercivity types are less prone to accidental erasure and
damage. Magnetic stripe cards require that the card come in direct
contact with the reader head causing wear and a shorter life span.
This direct contact requirement also can cause misreads due to dirt
and debris accumulation in the reader. Certain access control systems
allow the user to utilize their existing credit cards, eliminating the
need to purchase cards. The cards are low in cost but are easily
duplicated, are affected by outside magnetic fields, and the readers
require occasional cleaning to remove any dirt buildup on the read
heads.
A number of International Organization for Standardization standards,
ISO/IEC 7810, ISO/IEC 7811, ISO/IEC 7812, ISO/IEC 7813, ISO 8583 and
ISO/IEC 4909, define the physical properties of the card, including
size, flexibility, location of the mag-stripe, magnetic
characteristics, and data formats.They also provide the standards for
financial cards, including the allocation of card number ranges to
different card issuing institutions.
Macro
A defined set of actions or commands that can be manually executed by
the operator or is based on a trigger event.
Matching
Biometric data (e.g. fingerprints) are matched to another sample to
confirm a person’s identity (authentication). For example, useing
optic scanners to collect fingerprint minutiae, then create
mathematical templates based on that information for storage. New
input fingerprints are scanned and compared to the stored samples. If
the minutiae matching threshold is met, the person is authenticated.
The matching step is classified into 1:1 and 1:N matching according to
its purpose and/or the number of reference templates. 1:1 matching is
also called personal identification or verification. It is a procedure
in which a user claims his/her identity by means of an ID and proves
it with a fingerprint. The comparison occurs only once between the
input fingerprint image and the selected one from the database
following the claim by the user.
On the contrary, 1:N matching denotes a procedure where the system
determines the user's identity by comparing the input fingerprint with
the information in the database without asking for the user's claim. A
good example of this is AFIS(Automated Fingerprint Identification
System) frequently used in criminal investigation.
The output result of the matching step is whether or not the input
fingerprint is identical to the one being compared in the database.
Then how could the accuracy of the matching procedure be represented
in number? The simplest measures are FRR(False Reject Rate) and
FAR(False Accept Rate). The former is the rate of genuine user's
rejection and the latter is the rate of impostor's acceptance.
Memory Cards
Although referred to as smart cards, memory cards are typically much
less expensive and much less functional than microprocessor cards.
They contain erasable programmable read-only memory (EEPROM) and
read-only memory (ROM), as well as some address and security logic. In
the simplest designs, logic exists to prevent writing and erasing of
the data. More complex designs allow memory read access to be
restricted. Typical memory card applications are pre-paid telephone
cards and health insurance cards.
Mifare
Mifare is an interface for contact less smart cards and smart card
readers. It has been developed by Philips and influencing the ISO14443
Standard.
MIFARE Ultralight
Low-cost ICs that employ the same protocol as MIFARE Classic, Only 512
bits of memory (i.e. 64 bytes), without cryptographic security and
slightly different commands.
MIFARE Plus
Drop-in replacement for MIFARE Classic with certified security level
AES 128 based. 2Kbytes or 4Kbytes of memory, Security upgrade with
cards in the field.
MIFARE Classic
The MIFARE Classic card is fundamentally just a memory storage device,
where the memory is divided into segments and blocks with simple
security mechanisms for Access Control. The MIFARE Classic 1K offers
1024 bytes of data storage, split into 16 sectors; each sector is
protected by two different keys, called A and B. They can be
programmed for operations like reading, writing, increasing value
blocks etc.). MIFARE Classic 4K offers 4096 bytes split into forty
sectors, of which 32 are same size as in the 1K with eight more that
are quadruple size sectors. MIFARE Classic mini offers 320 bytes split
into five sectors. For each of these card types, 16 bytes per sector
are reserved for the keys and access conditions and can not normally
be used for user data. Also, the very first 16 bytes contain the
serial number of the card and certain other manufacturer data and are
read only. That brings the net storage capacity of these cards down to
752 bytes for Classic 1k, 3440 bytes for Classic 4k, and 224 bytes for
Mini.
Minutiae
The unique, measurable physical characteristics scanned as input and
stored for matching by biometric systems. For fingerprints, minutiae
include the starting and ending points of ridges, bifurcations and
ridge junctions among other features.
Minutiae Database
The database that contains all fingerprint templates in the system.
The minutiae database is contained within the image database.
Masking
Hiding or suppressing alarms that the operator does not wish to be
viewed.
MPG (Monitor Point Group)
A collection of monitor points that typically have been grouped for
common manageability.
NIST
Abbreviation for the National Institute for Standardization of
Technology, which is an agency of the US Federal Government which
establishes standards and guidelines for private and public sector
purposes.
NAT (Network address translation)
When a network device with a private IP address wants to send
information via the Internet, it must do so using a router that
supports NAT. Using this technique, the router can translate a private
IP address into a public IP address without the sending host’s
knowledge.
Non-cooperative User
An individual who is not aware that his/her biometric sample is being
collected. The phrase denotes a person who has not explicitly agreed
to provide biometric information.
Example: A traveler passing through a security line at an airport is
unaware that a camera is capturing his/her face image.
Network-enabled main controllers
The topology is nearly the same as described in the second and third
paragraphs. The same advantages and disadvantages apply, but the
on-board network interface offers a couple valuable improvements.
Transmission of configuration and users to the main controllers is
faster and may be done in parallel. This makes the system more
responsive and does not interrupt normal operations. No special
hardware is required in order to achieve redundant host PC setup: in
case the primary host PC fails, the secondary host PC may start
polling network controllers.
Odor Identification Technology
The body odor biometrics is based on the fact that virtually each
human smell is unique. The smell is captured by sensors that are
capable to obtain the odor from non-intrusive parts of the body such
as the back of the hand. Methods of capturing a person’s smell are
being explored by Mastiff Electronic Systems. Each human smell is made
up of chemicals known as volatiles. They are extracted by the system
and converted into a template.
The use of body odor sensors brings up the privacy issue as the body
odor carries a significant amount of sensitive personal information.
It is possible to diagnose some diseases or activities in the last
hours (like sex, for example) by analyzing the body odor.
Operator
Anyone with access to the application. The Administrator is also an
Operator, though generally distinguished in the documentation due to
the difference in responsibility and permissions.
Overt Collection
This term describes biometric sample collection where end users
(subjects) know they are being collected and at what location.
An example of an overt environment is the US-VISIT program where non-U.S.
citizens entering the United States submit their fingerprint data.
One-to-One
A phrase used in the biometrics community to describe a system that
compares one reference to one enrolled reference to make a decision.
typically, the phrase "one-to-one" refers to the verification task
(though not all verification tasks are truly one-to-one) and the
identification task can be accomplished by a series of one-to-one
comparisons.
One-to-Many
Fingerprint search that compares the minutiae from a candidate
fingerprint image against the fingerprint minutiae database to
determine whether or not the candidate exists in the database.
OEM (Original Equipment Manufacturer)
This is a designation for companies that manufacture equipment that is
then marketed and sold to other companies under their own names.
OEM Proprietary Formats
OEM formats are a unique data format reserved for the exclusive use of
an HID OEM customer. The OEM format structure is defined by the OEM
customer and HID. OEM formats are available in a number of different
data lengths with various data field definitions. The OEM format is
the HID customer's way of providing their customers with a unique
card, and unduplicated card numbers.
Optical Sensors
Optical sensors use arrays of photo-diode or photo-transistor
detectors to convert the energy in light incident on the detector into
electrical charge. The sensor package usually includes a
light-emitting-diode (LED) to illuminate the finger.
There are two detector types used by optical sensors,
charge-coupled-devices (CCD) and CMOS based optical imagers. CCD
detectors are sensitive to low light levels and are capable of making
excellent gray-scale pictures. However, CCD fabrication is relatively
expensive and neither low-light sensitivity or gray-scale imaging are
required for fingerprint recognition. CMOS optical imagers are
manufactured in quantity and can be made with some of the image
processing steps built into the chip resulting in a lower cost.
Optical sensors for fingerprints may be affected by a number of real
world factors such as stray light and surface contamination, possibly
even a fingerprint impression left by a prior user. Common
contaminates that deteriorate image quality include oil and dirt,
scratches on the sensor surface, and condensation or ice. Some
suppliers have tried to sidestep the contamination problem by directly
taking a 3D image from the surface of a finger. 3D imaging technology
is more hygienic but introduces a whole new set of problems and was
not included in this study.
Impostor prints are more of a problem for optical sensors than it is
for other detectors because it is relatively easy to present the
scanner with a convincing picture of a fingerprint. Suppliers have
come up with several techniques to validate a live finger. For example
optical sensors can be enhanced and made more resistant to deception
with Electro-Optical imaging. This works by placing a voltage across a
light-emitting polymer film. When a finger is presented, the ridges
provide a ground to the polymer surface creating a small current that
generating light. The fingerprint valleys remain dark so a high
contrast image is produced. The polymer is directly coupled to an
optical detector.
ONVIF (Open Network Video Interface Forum)
ONVIF is an open industry forum for the development of a global
standard for the interface of network video products.
PEM (Privacy Enhanced Mail)
An early standard for securing electronic mail. The PEM-format is
often used for representing an HTTPS certificate or certificate
request.
Palmprint
Palmprint is based on ridges, principal lines and wrinkles on the
surface of the palm
Ridges: When you look closely to you palm and fingers, you will notice
that the skin is not smooth, but has some sort of a pattern. You will
also notice that this pattern is actually formed by the raised portion
of the skin. This raised portion is called ridges. When pattern is
captured from your palm, then it is called a palmprint, and when
captured from the tip of the finger then it is called fingerprints.
Advantages of Palmprint Biometrics:
• Since the palm area is much larger, hence more distinctive features
can be captured compared to fingerprints. This makes it more even more
suitable in identification systems than fingerprints.
Disadvantages of Palmprint Biometrics:
• The palmprint scanners are usually bulkier and expensive since they
need to capture a larger area than the fingerprints scanners.
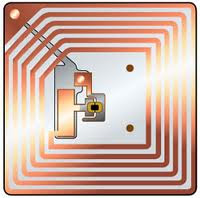 Passive RFID tag
Passive RFID tag
A passive tag is an RFID tag that does not contain a battery; the
power is supplied by the reader. When radio waves from the reader are
encountered by a passive RFID tag, the coiled antenna within the tag
forms a magnetic field. The tag draws power from it, energizing the
circuits in the tag. The tag then sends the information encoded in the
tag's memory. The advantages of a passive RFID tag are: The tag
functions without a battery; these tags have a useful life of twenty
years or more.
The tag is typically much less expensive to manufacture
The tag is much smaller (some tags are the size of a grain of rice).
These tags have almost unlimited applications in consumer goods and
other areas. The major disadvantages of a passive RFID tag are:
The tag can be read only at very short distances, typically a few feet
at most. This greatly limits the device for certain applications. It
may not be possible to include sensors that can use electricity for
power. The tag remains readable for a very long time, even after the
product to which the tag is attached has been sold and is no longer
being tracked.
PIV-card
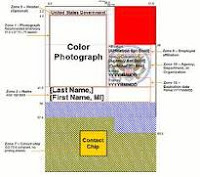 |
| PIV Card |
Personal Identity Verification Card required to be issued to all US
Federal employees and contractors under HSPD-12.
Precise Match-on-Card
The company's technology for storing and matching fingerprints on
smart cards. The smart card has built-in software which matches the
template saved on the card against the input biometric image. As such,
the template never leaves the secure environment of the smart card,
protecting both the biometric information and the user's personal
privacy.
Palm Vein Identification Technology
The pattern of blood veins is unique to every individual, even among
identical twins. Palms have a broad and complicated vascular pattern
and thus contain a wealth of differentiating features for personal
identification. Furthermore, it will not vary during the person's
lifetime. It is a very secure method of authentication because this
blood vein pattern lies under the skin. This makes it almost
impossible for others to read or copy.
An individual's vein pattern image is captured by radiating his/her
hand with near-infrared rays. The reflection method illuminates the
palm using an infrared ray and captures the light given off by the
region after diffusion through the palm. The deoxidized hemoglobin in
the in the vein vessels absorbs the infrared ray, thereby reducing the
reflection rate and causing the veins to appear as a black pattern.
This vein pattern is then verified against a preregistered pattern to
authenticate the individual.
As veins are internal in the body and have a wealth of differentiating
features, attempts to forge an identity are extremely difficult,
thereby enabling a high level of security. In addition, the sensor of
the palm vein device can only recognize the pattern if the deoxidized
hemoglobin is actively flowing within the individual's veins.
This system is not dangerous; a near infrared is a component of
sunlight: there is no more exposure when scanning the hand than by
walking outside in the sun.
Password
The permission level of the operator environment. Required for
permission to log on to the application.
Password Bank
A database for storing username, password and other personal
information, to be released upon verification of an individual's
identity.
Portrait
Vertical orientation of pages, screen display or badges
Pressure Sensors
Pressure sensing scanners can be made very thin and are often used
in electronic devices. Early pressure sensing scanners had to make a
tradeoff between durability and quality because any protective layer
on the detector surface would diminish the contrast of the impression.
There are two types of pressure sensing detectors available,
conductive film detectors and micro electro-mechanical devices (MEMS).
Conductive film sensors use a double-layer electrode on flexible
films. MEMS is a newer technology that uses extremely tiny silicon
switches on a silicon chip. When a fingerprint ridge touches a switch,
it closes and is detected electronically
Pre-Alarm Held
An alert given before an opened door reports “held open” alarm.
Physical/Physiological Biometric
A biometric that is characterized by a physical characteristic rather
than a behavioral trait. (contrast with behavioral biometric)
Proximity
The most common reader is called Proximity. These systems use cards or
tokens as a means of identification. As the name implies, no direct
contact is required between the card and the reader for the system to
operate, the card must only be in the proximity of the reader. The
read range will vary depending upon the card/token and the type of
reader, from 1/2 inch to up to 33 feet. The reader generates an RF
field which causes specially designed wires in the card to resonate,
transferring the card information to the reader. These cards are
immune to electromagnetic and RF interference, and they can offer
"hands free" operation.
Proximity card(Proximity Access card)
Proximity card (or Prox Card) is a generic name for contactless
integrated circuit devices used for security access. It can refer to
the older 125 kHz devices or the newer 13.56 MHz contactless RFID
cards, most commonly known as contactless smartcards.
Modern proximity cards are covered by the ISO/IEC 14443 (Proximity
Card) standard. There is also a related ISO/IEC 15693 (Vicinity Card)
standard. Proximity cards are powered by resonant energy transfer and
have a range of 0-3 inches in most instances. The user will usually be
able to leave the card inside a wallet or purse. Proximity cards use
an LC circuit. An IC, capacitor, and coil are connected in parallel.
The card reader presents a field that excites the coil and charges the
capacitor, which in turn energizes and powers the IC. The IC then
transmits the card number via the coil to the card reader. The card
readers communicate in Wiegand protocol that consists of a data 0 and
a data 1 circuit (or binary or simple on/off (digital) type circuit).
The earliest cards were 26 bit. As demand has increased bit size has
increased to continue to provide unique numbers. Often, the first
several bits can be made identical; these are called facility or site
code. The idea is that company Alice has a facility code of xn and a
card set of 0001 through 1000 and company Bob has a facility code of
yn and a card set also of 0001 through 1000.
Proximity card Reader
A Proximity reader radiates a 1" to 20" electrical field around
itself. Cards use a simple LC circuit. When a card is presented to the
reader, the reader's electrical field excites a coil in the card. The
coil charges a capacitor and in turn powers an integrated circuit. The
integrated circuit outputs the card number to the coil which transmits
it to the reader.
 A
common proximity format is 26 bit Wiegand. This format uses a facility
code, sometimes also called a site code. The facility code is a unique
number common to all of the cards in a particular set. The idea is
that an organization will have their own facility code and a set of
numbered cards incrementing from 1. Another organization has a
different facility code and their card set also increments from 1.
Thus different organizations can have card sets with the same card
numbers but since the facility codes differ, the cards only work at
one organization. This idea worked fine for a while but there is no
governing body controlling card numbers, and different manufacturers
can supply cards with identical facility codes and identical card
numbers to different organizations. Thus there is a problem of
duplicate cards. To counteract this problem some manufacturers have
created formats beyond 26 bit Wiegand that they control and issue to
organizations.
A
common proximity format is 26 bit Wiegand. This format uses a facility
code, sometimes also called a site code. The facility code is a unique
number common to all of the cards in a particular set. The idea is
that an organization will have their own facility code and a set of
numbered cards incrementing from 1. Another organization has a
different facility code and their card set also increments from 1.
Thus different organizations can have card sets with the same card
numbers but since the facility codes differ, the cards only work at
one organization. This idea worked fine for a while but there is no
governing body controlling card numbers, and different manufacturers
can supply cards with identical facility codes and identical card
numbers to different organizations. Thus there is a problem of
duplicate cards. To counteract this problem some manufacturers have
created formats beyond 26 bit Wiegand that they control and issue to
organizations.
In the 26 bit Wiegand format, bit 1 is an even parity bit. Bits 2-9
are a facility code. Bits 10-25 are the card number. Bit 26 is an odd
parity bit. Other formats have a similar structure of a leading
facility code followed by the card number and including parity bits
for error checking.
PIN
A Personal Identification Number assigned to a user. It is used either
by itself or in conjunction with a card.
Ping
Ping is a basic network program used diagnostically to check the
status of a network host or device. Ping can be used to see if a
particular network address (IP address or host name) is occupied or
not, or if the host at that address is responding normally. Ping can
be run from e.g. the Windows Command prompt or the command line in
Unix.
Port forwarding
Port forwarding or port mapping commonly refers to the change of
destination address and/or port on the packet with subsequent regular
routing in a network address translator (NAT) gateway to reach a host
within a masqueraded, typically private, network based on the port
number on which it was received from the originating host. It may also
refer to replaying the packet or stream through a secondary socket
(e.g. like rinetd) to reach its intended destination.
The technique is used to permit communications by external hosts with
services provided within a private local area network (LAN).
Port forwarding allows remote computers (e.g., public machines on the
Internet) to connect to a specific computer within a private LAN.
For example:
•Running a public HTTP server within a private LAN (port 80)
•Permitting Secure Shell access on the private LAN from the Internet
(port 22)
•Permitting FTP access to hosts on a private LAN from the Internet
(port 21)
Port forwarding can also be used within a single machine. Port
forwarding is necessary for a standalone computer if any of the
following conditions are true:
•The computer is using a shared IP address.
•Internet Connection Sharing is enabled.
•A router is being used with network address translation (NAT)
enabled.
Purge database
This function is used to remove the unnecessary data from the
database. For removing the data select date, so that all the access
transactions which occurred before that date will be erased from the
database.
QoS (Quality of Service)
QoS provides the means to guarantee a certain level of a specified
resource to selected traffic on a network. Quality can be defined as
e.g. a maintained level of bandwidth, low latency, no packet losses,
etc. The QoS in Axis network video products marks the data packets for
various types of network traffic originating from the product. This
makes it possible for network routers and switches to e.g. reserve a
fixed amount of bandwidth for these types of traffic
Reader
A device that can read the encoding on a card or badge.
RS232
RS-232 (Recommended Standard 232) is a standard for serial binary
single-ended data and control signals connecting between a DTE (Data
Terminal Equipment) and a DCE (Data Circuit-terminating Equipment). It
is commonly used in computer serial ports.
Mode of Operation: SINGLE-ENDED
Total Number of Drivers and Receivers on One Line: 1 DRIVER-1 RECVR
Maximum Cable Length: 15Mtr (50 FT).
Maximum Data Rate: 20kb/s
Receiver Input Resistance: 3KΩ - 7 KΩ
RS 485 / EIA-485
RS485 are serial communication methods for computers and devices. Most
versatile communication standard in the standard series defined by the
EIA, as it performs well on all four points. That is why RS485 is
currently a widely used communication interface in data acquisition
and control applications where multiple nodes communicate with each
other.
Max number of drivers/receivers : 32
Physical Media Twisted : Pair
Modes of operation : half duplex
Available Signals Tx+/Rx+, Tx-/Rx- (Half Duplex) & Tx+, Tx-, Rx+, Rx-
(Full Duplex)
Network topology: Point-to-point, Multi-dropped, Multi-point
Max distance (acc. standard): 1200 m (4000 feet)
Max speed at 12 m: 35 Mbs & 1200 m: 100 kbs
Receiver input resistance: ≥12 kΩ
Driver load impedance: 54 Ω
RS485 is the only of the interfaces capable of internetworking
multiple transmitters and receivers in the same network. When using
the default RS485 receivers with an input resistance of 12 kΩ it is
possible to connect 32 devices to the network. Currently available
high-resistance RS485 inputs allow this number to be expanded to 256.
RS485 repeaters are also available which make it possible to increase
the number of nodes to several thousands, spanning multiple
kilometers.
Remote Host
A system where the main computer that controls the system is remotely
located. It allows a single computer to control multiple systems.
Reference Template
Data that represents the biometric measurement of an enrollee used by
a biometric system for comparison against subsequently submitted
biometric samples.
Registration
Process of registering biometric data with a Fingerprint
Identification Unit (FIU) or other biometric system.
Rejection/False Rejection
When a biometric system fails to identify an enrollee or fails to
verify the legitimate claimed identity of an enrollee. Also known as a
Type I error.
Response Time/Processing Time
The time period required by a biometric system to return a decision on
identification or verification of a biometric sample.
Retinal Biometrics
Retinography/Retinal Biometrics is a sophisticated means for
identifying people by the pattern of blood vessels on the retina (the
innermost coat of the back part of the eye). It requires the use of a
special scanner about the size of a shoe-box that can map the unique
pattern of blood vessels on the retina. The pattern is so complex that
even identical twins do not have the same blood vessel configuration.
Those who favor its use claim Retinography has an error rate of only
one in a million.
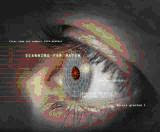 Retina
Scanning
Retina
Scanning
A retinal scanner uses infrared light for mapping. As a person looks
into the eyepiece, an invisible beam of low-energy infrared light
traces a circular path on the retina at the back of the eye. The
blood-filled capillaries absorb more of the infrared light than the
surrounding tissue. Because of this, there is a variation in the
intensity of the reflection. The scanner measures this reflection at
320 points along the beam path. It then assigns an intensity grade
between zero and 4,095. The resulting numbers are compressed into an
80-byte computer code. This code can then be compared with patterns
that have already been entered into the computer's database.
Retina scans are already in use in the Pentagon and government and
corporate organizations where people need to be identified before they
can enter an area. New concerns about security from terrorism and bank
and credit card fraud have caused many organizations to think
seriously of using retina scans or other biometric means to identify
people at airports and ATM machines.
RF Sensors
A low radio frequency (RF) signal is applied to the user’s finger and
then read by the detector array, with each pixel operating like a tiny
antenna. The advantage of this detector is that it reads the
fingerprint from the dermal layer underneath the surface making it
less susceptible to damaged or dry fingertips.
Radio frequency identification (RFID)
Radio frequency identification (RFID) is a generic term for
technologies that use radio waves to automatically identify people or
objects. It commonly works with a compute information system as
advanced means to control or manage terminal articles or people.
RFID is composed of microchip and antenna with various encapsulations
to adapt different environment in application. The antenna enables the
chip to communicate with the identification information to a reader in
air by contactless digital information transfer. For long lifespan and
low cost thinking, most of RFID product in common use are passive RFID,
it means no battery enclosed in, and it get the power from
corresponding frequency wave energy of reader.
RFID is a new technique emerging to business application with 10ten
year. We have great confidence from these years experience and
progress with process of innovation which rapidly accumulated.
Nevertheless, the advent of high-performance, facile, low-cost, RFID
technology is absolutely central to the ability to conduct information
warfare and information operations today. applications for RFID: RFID
is used for everything from tracking cows and pets to triggering
equipment down oil wells. It may sound trite, but the applications are
limited only by people's imagination. The most common applications are
payment systems (Mobil Speedpass and toll collection systems, for
instance), access control and asset tracking. Increasingly, retail/CPG
and pharma companies are looking to use RFID to track goods within
their supply chain, to work in process and for other applications.
Reverse port forwarding
Reverse port forwarding, or reverse port tunnelling, is
done by two components, usually software-based, where one component
acts as a session-server—listening on a session-port, while the other
component acts as a session-client to the session-server
component—connecting to the session-server. After a session is
established, the session-server will often listen on (accept
connections on) a port that is to be forwarded, and when a connection
is made to this port, the connection traffic will be forwarded to the
session-client (through the session-connection that was previously
initiated by the session-client), usually with a destination of the
session-client machine or another machine accessible from the
session-client.
A common situation where this type of forwarding is used is where a
port needs to be accessed that is on a machine located behind a
gateway/router or firewall that is not configurable by those wanting
to access that port. This functionality is built-in to some
implementations of SSH (Secure Shell), and there are also software
systems available that are designed more specifically for this type of
forwarding.
RTCP (Real-Time Control Protocol)
RTCP provides support for real-time conferencing of groups of any size
within an intranet. This support includes source identification and
support for gateways like audio and video bridges as well as
multicast-to-unicast translators.
It offers quality-of-service feedback from receivers to the multicast
group as well as support for the synchronization of different media
streams.
RTP (Real-Time Transport Protocol)
RTP is an Internet protocol for the transport of real-time data, e.g.
audio and video. It can be used for media-on-demand as well as
interactive services such as Internet telephony.
RTSP (Real Time Streaming Protocol)
RTSP is a control protocol, and a starting point for negotiating
transports such as RTP, multicast and Unicast, and for negotiating
codecs.
RTSP can be considered a “remote control” for controlling the media
stream delivered by a media server. RTSP servers typically use RTP as
the protocol for the actual transport of audio/video data.
Ridge
The raised skin areas which make up a fingerprint
Server
In general, a server is a computer program that provides services to
other computer programs in the same or other computers. A computer
running a server program is also frequently referred to as a server.
In practice, the server may contain any number of server and client
programs. A web server is the computer program that supplies the
requested HTML pages or files to the client (browser).
Switch
A switch is a network device that connects network segments together,
and which selects a path for sending a unit of data to its next
destination. In general, a switch is a simpler and faster mechanism
than a router, which requires knowledge about the network and how to
determine the route. Some switches include the router function.
Subnet & subnet mask
A subnet is an identifiably separate part of an organization's
network. Typically, a subnet may represent all the machines at one
geographic location, in one building, or on the same local area
network (LAN). Having an organization's network divided into subnets
allows it to be connected to the Internet with a single shared network
address.
The subnet mask is the part of the IP address that tells a network
router how to find the subnet that the data packet should be delivered
to. Using a subnet mask saves the router having to handle the entire
32-bit IP address; it simply looks at the bits selected by the mask.
SSL/TLS (Secure Socket Layer/Transport Layer Security)
These two protocols (SSL is succeeded by TLS) are cryptographic
protocols that provide secure communication on a network. SSL is
commonly used over HTTP to form HTTPS, as used e.g. on the Internet
for electronic financial transactions. SSL uses public key
certificates to verify the identity of the server.
Strong Passwords
A strong password is sufficiently long, random, or otherwise
producible only by the user who chose it, that successfully guessing
it will require too long a time. The length of time deemed to be too
long will vary with the attacker, the attacker's resources, the ease
with which a password can be tried, and the value of the password to
the attacker. A student's password might not be worth more than a few
seconds of computer time, whilst a password controlling access to a
large bank's electronic money transfer system might be worth many
weeks of computer time.
Examples of stronger passwords include:
t3wahSetyeT4
4pRte!ai@3
#3kLfN2x
MoOoOfIn245679
Semi-intelligent readers
Have all inputs and outputs necessary to control door hardware (lock,
door contact, exit button), but do not make any access decisions. When
a user presents a card or enters PIN, the reader sends information to
the main controller and waits for its response. If the connection to
the main controller is interrupted, such readers stop working or
function in a degraded mode. Usually semi-intelligent readers are
connected to a control panel via an RS-485 bus.
Serial controllers
Controllers are connected to a host PC via a serial RS485
communication line (or via 20mA current Loop in some older systems).
External RS-232/485 converters or internal RS-485 cards have to be
installed as standard PCs do not have RS-485 communication ports. In
larger systems multi-port serial IO boards are used, Digi
International being one of most popular options.
Advantages:
RS-485 standard allows long cable runs, up to 4000 feet (1200 m)
Relatively short response time. The maximum number of devices on an
RS-485 line is limited to 32, which means that the host can frequently
request status updates from each device and display events almost in
real time.
High reliability and security as the communication line is not shared
with any other systems.
Disadvantages:
• RS-485 does not allows Star-type wiring unless splitters are used
• RS-485 is not well suited for transferring large amounts of data
(i.e. configuration and users). The highest possible throughput is
115.2 kbit/s, but in most system it is downgraded to 56.2 kbit/s or
less to increase reliability.
• RS-485 does not allow host PC to communicate with several
controllers connected to the same port simultaneously. Therefore in
large systems transfers of configuration and users to controllers may
take a very long time and interfere with normal operations.
• Controllers cannot initiate communication in case of an alarm. The
host PC acts as a master on the RS-485 communication line and
controllers have to wait till they are polled.
• Special serial switches are required in order to build a redundant
host PC setup.
• Separate RS-485 lines have to be installed instead of using an
already existing network infrastructure.
• Cable that meets RS-485 standards is significantly more expensive
than the regular Category 5 UTP network cable.
• Operation of the system is highly dependent on the host PC. In case
the host PC fails, events from controllers are not retrieved and
functions that required interaction between controllers (i.e. anti-passback)
stop working.
Serial main and sub-controllers
All door hardware is connected to sub-controllers (Door controllers or
door interfaces). Sub-controllers usually do not make access
decisions, and forward all requests to the main controllers. Main
controllers usually support from 16 to 32 sub-controllers.
Advantages:
• Work load on the host PC is significantly reduced, because it only
needs to communicate with a few main controllers.
• The overall cost of the system is lower, as sub-controllers are
usually simple and inexpensive devices.
• All other advantages listed in the Serial controllers index
advantage apply.
Disadvantages:
• Operation of the system is highly dependent on main controllers. In
case one of the main controllers fails, events from its
sub-controllers are not retrieved and functions that require
interaction between sub controllers (i.e. anti-passback) stop working.
• Some models of sub-controllers (usually lower cost) have no memory
and processing power to make access decisions independently. If the
main controller fails, sub-controllers change to degraded mode in
which doors are either completely locked or unlocked and no events are
recorded. Such sub-controllers should be avoided or used only in areas
that do not require high security.
• Main controllers tend to be expensive, therefore such topology is
not very well suited for systems with multiple remote locations that
have only a few doors.
• All other RS-485-related disadvantages listed in the Serial
controllers index apply.
Serial main Controllers & Intelligent Readers:
All
door hardware is connected directly to intelligent or semi-intelligent
readers. Readers usually do not make access decisions, and forward all
requests to the main controller. Only if the connection to the main
controller is unavailable, the readers use their internal database to
make access decisions and record events. Semi-intelligent reader that
have no database and cannot function without the main controller
should be used only in areas that do not require high security. Main
controllers usually support from 16 to 64 readers. All advantages
and disadvantages are the same as the ones listed in the Serial
main and sub-controllers paragraph.
Serial Controllers with Terminal Servers
In spite of the rapid development and increasing use of computer
networks, access control manufacturers remained conservative and did
not rush to introduce network-enabled products.
When pressed for solutions with network connectivity, many chose the
option requiring less effort: addition of a terminal server, a device
that converts serial data for transmission via LAN or WAN. Terminal
servers manufactured by Lantronix and Tibbo Technology are popular in
the security industry.
Advantages:
• Allows utilizing existing network infrastructure for connecting
separate segments of the system.
• Provides convenient solution in cases when installation of an RS-485
line would be difficult or impossible.
Disadvantages:
• Increases complexity of the system.
• Creates additional work for installers: usually terminal servers
have to be configured independently, not through the interface of the
access control software.
• Serial communication link between the controller and the terminal
server acts as a bottleneck: even though the data between the host PC
and the terminal server travels at the 10/100/1000Mbit/s network speed
it then slows down to the serial speed of 112.5 kbit/s or less. There
are also additional delays introduced in the process of conversion
between serial and network data.
• All RS-485-related advantages and disadvantages also apply.
Signature Recognition
Signature recognition systems measure and analyze the physical
activity of signing such as stroke order, pressure applied and the
speed of the pen while signing. It differs substantially from the way
signature recognition on paper is done which compares the visual
aspects of the signature.
Speaker Identification Technology
Speaker recognition (also known as voice recognition) is the
computing task of recognizing people (which may involve identifying
them and/or authenticating their identity) from their voices. Such
systems extract features from speech, model them, and use them to
recognize the person from his/her voice.
Note that there is a difference between speaker recognition
(recognizing who is speaking) and speech recognition
(recognizing what is being said). These two terms are frequently
confused, as is voice recognition. Voice recognition is a
synonym for speaker, and thus not speech, recognition.
Speaker recognition has a history dating back some four decades, where
the output of several analog filters was averaged over time for
matching. Speaker recognition uses the acoustic features of speech
that have been found to differ between individuals. These acoustic
patterns reflect both anatomy (e.g., size and shape of the throat and
mouth) and learned behavioral patterns (e.g., voice pitch, speaking
style). This incorporation of learned patterns into the voice
templates (the latter called "voiceprints") has earned speaker
recognition its classification as a "behavioral biometric."
Save
An action to record information in the database. See Download in this
post.
Spoofing
Spoofing refers to the ability to fool a biometric sensor into
recognizing an illegitimate user as a legitimate user (verification)
or into missing an identification of someone that is in the database.
Silicon technology scanners:
Silicon technology has gained considerable acceptance since its
introduction in the late 90's. Most silicon, or chip, technology is
based on DC capacitance. The silicon sensor acts as one plate of a
capacitor, and the finger is the other. The capacitance between platen
and the finger is converted into an 8-bit grayscale digital image.
With the exception of AuthenTec, whose technology employs AC
capacitance and reads to the live layer of skin, all silicon
fingerprint vendors use a variation of this type of capacitance.
Silicon generally produces better image quality, with less surface
area, than optical. Since the chip is comprised of discreet rows and
columns - between 200-300 lines in each direction on a 1cmx1.5cm wafer
- it can return exceptionally detailed data. The reduced size of the
chip means that costs should drop significantly, now that much of the
R&D necessary to develop the technology is bearing fruit. Silicon
chips are small enough to be integrated into many devices which cannot
accommodate optical technology.
Silicon's durability, especially in sub-optimal conditions, has yet to
be proven. Although manufacturers use coating devices to treat the
silicon, and claim that the surface is 100x more durable than optical,
this has to be proven. Also, with the reduction in sensor size, it is
even more important to ensure that enrolment and verification are done
carefully - a poor enrollment may not capture the center of the
fingerprint, and subsequent verifications are subject to the same type
of placement. Many major companies have recently moved into the
silicon field. Infineon (the semiconductor division of Siemens) and
Sony have developed chips to compete with Veridicom (a spin-off of
Lucent), the leader in silicon technology.
Shunt
Length of time an input will be ignored when it goes active during an
access granted event. This only applies to inputs that are specified
as the Door Contact.
Smart Card
A smart card, chip card, or integrated circuit card (ICC), is
any pocket-sized card with embedded integrated circuits. There are two
broad categories of ICCs. Memory cards contain only non-volatile
memory storage components, and perhaps dedicated security logic.
Embedded microchip cards contain volatile memory. The card is made of
plastic, generally polyvinyl chloride, but sometimes acrylonitrile
butadiene styrene or polycarbonate. which can be used to store
information about the cardholder or record card transactions as they
occur.
Dimensions are normally credit card size. ID-1 of the ISO/IEC 7810
standard defines them as nominally 85.60 by 53.98 millimetres (3.370 ×
2.125 in). Another popular size is ID-000 which is nominally 25 by 15
millimetres (0.984 × 0.591 in) (commonly used in SIM cards).
Both are 0.76 millimetres (0.030 in) thick.
Smart Cards Advantages
Compared to magnetic stripe cards, smart cards have many advantages:
• Smart cards can hold up to 32 KB of data while magnetic cards as
seen earlier can hold only around 1000 bits. This allows the
card-transaction participants (card company, acquiring bank, issuing
bank, retailers etc.) to store a lot of additional information on the
card.
• Data on a smart card can be protected against unauthorized viewing.
As a result of this confidential data (PIN, Passwords) can be stored
on a smart card. This means, merchants do not have to go online every
time to authenticate a transaction.
• A single smart card can house multiple applications. Just one card
can be used as your license, passport, credit card, ATM card, ID Card
etc.
• Life of a smart card is longer.
• Smart cards cannot be easily replicated and are, as a general rule
much more secure that magnetic stripe cards.
Given these advantages, smart cards have really caught on in the
telephony segment. But unfortunately, they have not been as successful
in the financial cards segment. The only thing holding back the
widespread use of smart cards in this sector is the amount of money
invested by various players in the magnetic stripe card infrastructure
and the slightly higher cost of smart cards.
Smart Capture
Smart Capture is a feature ensures quality fingerprint scanning of
difficult fingers. By automatically adjusting the brightness of the
sensor, Smart Capture allows the SecuGen fingerprint reader to capture
high quality fingerprints from a wide range of traditionally difficult
fingers, including those from dry, wet, scarred or aged skin, and even
in bright ambient conditions such as under direct sunlight.
Static Fingerprint Reader/Sensor
A Static Fingerprint Reader/Sensor requires the user to place the
finger motionless on a surface. The sensor array must be as large as
the area of the image to be captured.
Swipe Fingerprint Reader/Sensor
A Swipe Fingerprint Reader/Sensor requires the user drag the upper
part of the finger across the sensor. The complete image is pieced
together by accumulating the partial image as the finger moves across
the scan area.
Sub-controller
One of a series of circuit boards that communicates information about
field devices like readers, contacts, motion detectors, etc., upstream
to the SSP. (RSC-1, RSC-2, RSC-T, ISC-16, and OSC-16).
Stand alone Controller/Reader
A system where the entire system is contained in the Controller / card
reader.
Shunt time
When a door is released the status switch is automatically "shunted"
for a period of time to allow the person to enter/exit. If the time is
exceeded a door held open signal will occur.
Status switch/ Magnetic Contact(MC)
A magnetic contact mounted on the controlled door. It is used to
detect door held or door forced.
Tamper
(1)A digital input that, if open, signals a cabinet tamper alarm at
the device.
(2)A digital input that signals power loss alarm at the device.
Template:
A digital representation of an individual’s distinct characteristics,
representing information extracted from a biometric sample. BioCert
devices convert fingerprint minutiae into mathematical templates.
Templates are used during biometric authentication as the basis for
comparison.
Tokens:
A physical device that an authorized user of computer services is
given to aid in authentication. Hardware tokens are often small enough
to be carried in a pocket or purse. Some may store cryptographic keys,
like a digital signature, or biometric data, like a fingerprint.
Time Schedules
Consist of time ranges that are associated with days or holidays. Time
Schedules are used in connection with access levels and often as
trigger events.
Time zones
"Schedules" that allow cards to function or not function depending on
the time of day. This is used to limit access to the facility. The
schedule may include not only time but which days of the week a card
is valid.
Time and Attendance Systems:
Time and attendance has always been a problem in some industries.
Biometrics can effectively eliminate problems with buddy clocking by
ensuring that the employee in question is present.
Thermal Sensors
Thermal sensors use the same pyro-electric material that is used in
infrared cameras. When a finger is presented to the sensor, the
fingerprint ridges make contact with the sensor surface and the
contact temperature is measured, the valleys do not make contact and
are not measured. A fingerprint image is created by the
skin-temperature ridges and the ambient temperature measure for
valleys.
The biggest drawback of this technique is that the temperature change
is dynamic and it only takes about a tenth of a second for the sensor
surface touching ridges and valleys to come to the same temperature,
erasing the fingerprint image. Additionally, this technology has many
of the same contamination and wear issues as other sensors. While it
can operation over a wide range of temperatures, if the ambient
temperature is close to the finger surface temperature the sensor
requires heating to create a temperature difference of at least 1
degree Centigrade.
True Reject Rate
The true reject rate is a statistic used to measure biometric
performance when performing the verification task. It refers to the
percentage of times a system (correctly) rejects a false claim of
identity.
For example, Mr. X claims to be Mr. Y and the system rejects the claim
(as it should).
True Accept Rate
The true accept rate is a statistic used to measure biometric
performance when performing the verification task. It is the
percentage of times a system (correctly) verifies a true claim of
identity.
For example, Mr. X claims to be Mr. X, and the system verifies the
claim.
Trigger
A system event that causes another event or macro to occur.
Threshold
The acceptance or rejection of biometric data is dependent on the
match score falling above or below the threshold. The threshold is
adjustable so that the biometric system can be more or less strict,
depending on the requirements of any given biometric application.
Type I Error
The failure of a fingerprint identification system when it does not
match a candidate fingerprint pattern with its mating fingerprint
pattern (in other words, a failure to make a match that should have
been made).
Type II Error
The failure of a fingerprint identification system when it matches a
candidate fingerprint pattern with a non-mating fingerprint pattern
(in other words, making a match that should not have been made).
Turnstile
A turnstile, also called a baffle gate, is a form of gate which allows
one person to pass at a time. It can also be made so as to enforce
one-way traffic of people, and in addition, it can restrict passage
only to people who insert a coin, a ticket, a pass, or similar. Thus a
turnstile can be used in the case of paid access (sometimes called a
faregate when used for this purpose), for example public transport as
a ticket barrier or a pay toilet, or to restrict access to authorized
people, for example in the lobby of an office building.
Turnstiles are used at a wide variety of settings, including stadiums,
amusement parks, museums, mass transit stations, office lobbies,
retail sites, cafeterias, temporary exhibits, casinos and souvenir
stands, to name but a few.
Turnstiles - Full-height
The High Entrance/Exit Turnstile (HEET), or full-height turnstile, is
a larger version of the turnstile, commonly 7-foot (2.1 m) high,
similar in operation to a revolving door, which eliminates the
possibility (inherent in the waist-high style) of anyone jumping over
a turnstile unit. It is also known as an "iron maiden", after the
medieval torture device of the same name, or as "high-wheel".
TCP and UDP port
A port is an application-specific or process-specific software
construct serving as a communications endpoint, providing a
multiplexing service. It is used by Transport Layer protocols of the
Internet Protocol Suite, such as Transmission Control Protocol (TCP)
and User Datagram Protocol (UDP). A specific port is identified by its
number, commonly known as the port number, the IP address with which
it is associated, and the protocol used for communication.
The reason for having ports are that virtually all modern computers
support multitasking. Thus, on a typical computer, there will be
multiple programs which need to contact other programs on other
computers over the network all at the same time. Ports enable multiple
programs to share a single physical network connection simultaneously,
as opposed to having only one program using the connection for a long
period of time.
ransport Layer protocols, such as TCP, UDP, SCTP, and DCCP, specify a
source and destination port number in their packet headers. A port
number is a 16-bit unsigned integer, thus ranging from 0 to 65535. A
process associates its network input or output channels each with a
particular port number, a process known as binding, to send and
receive data. The operating system's networking software has the task
of transmitting outgoing data from all application ports onto the
network, and forwarding arriving network packets to a process by
matching the packets IP address and port numbers.
An example for the use of ports is the Internet mail system. A server
used for sending and receiving email generally needs two services. The
first service is used to transport email to and from other servers.
This is accomplished with the Simple Mail Transfer Protocol (SMTP).
The SMTP service application usually listens on TCP port 25 for
incoming requests. The second service is the Post Office Protocol
(POP) which is used by e-mail client applications on user's personal
computers to fetch email messages from the server. The POP service
listens on TCP port number 110. Both services may be running on the
same host computer, in which case the port number distinguishes the
service that was requested by a remote computer, be it a user's
computer or another mail server.
While the listening port number of a server is well defined (IANA
calls these the well known ports), the client's port number is often
chosen from the dynamic port range (see below). In some applications,
the client and the server each use specific port numbers assigned by
the IANA. A good example of this is DHCP in which the client always
uses UDP port 68 and the server always uses UDP port 67.
Port numbers can occasionally be seen in the Uniform Resource Locator
(URL) of a website or other services. By default, HTTP uses port 80
and HTTPS uses port 443, but a URL like
http://www.example.com:8000/blah/ specifies that the web site is
served by the HTTP server on port 8000. The active transport layer
protocol ports may be discovered on many operating systems (Windows,
Unix-like, z/OS) with the command line netstat -a.
The port numbers are divided into three ranges: the well-known ports,
the registered ports, and the dynamic or private ports. The well-known
ports are those from 0 through 1023. Examples include:
21: FTP
23: Telnet
53: Domain Name System
80: World Wide Web HTTP
119: Network News Transfer Protocol
443: HTTP over Transport Layer Security / Secure Sockets Layer
445: microsoft-ds, Server Message Block over TCP
The registered ports are those from 1024 through 49151.
Unicast
Communication between a single sender and a single receiver over a
network. A new connection is established for each new user.
UPnPTM
A set of computer network protocols that allows the automatic
peer-to-peer detection of devices on the network. UPnP is promoted by
the UPnP Forum.
Ultrasonic Sensors
Ultrasonic scanners have an advantage of being able to see beneath the
skin. This provides not only verification of a live finger, it
provides more information as a biometric measure. But this technology
is slow, expensive, bulky, and too data intensive for most access
control applications.
Ultrasound technology scanners:
Ultrasound technology, though considered perhaps the most accurate of
the fingerprint technologies, is not yet widely used. It transmits
acoustic waves and measures the distance based on the impedance of the
finger, the platen, and air. Ultrasound is capable of penetrating dirt
and residue on the platen and the finger, countering a main drawback
to optical technology.
Uncooperative User
The term uncooperative user refers to an individual who actively tries
to deny the capture of his/her biometric data.
For example, a prisoneer who mutilates his finger upon apprehension to
prevent the recognition of his/her identity via fingerprint.
USB
(Universal Serial Bus) A plug-and-play interface between a computer
and peripheral devices (scanners, printers etc).
USB flash drive
A USB flash drive consists of a flash memory data storage device
integrated with a USB (Universal Serial Bus) 1.1 or 2.0 interface. USB
flash drives are typically removable and rewritable, and physically
much smaller than a floppy disk. Most weigh less than 30 g (1 oz).
They are smaller, faster, have thousands of times more capacity, and
are more durable and reliable because of their lack of moving parts.
The memory storage was based on earlier EPROM and EEPROM technologies.
Most flash drives ship preformatted with the FAT or FAT 32 file
system.
Validation
The process of demonstrating that the system under consideration meets
in all respects the specification of that system.
VPN (Virtual Private Network)
This creates a secure “tunnel” between the points within the VPN. Only
devices with the correct "key" will be able to work within the VPN.
The VPN network can be within a company LAN (Local Area Network), but
different sites can also be connected over the Internet in a secure
way. One common use for VPN is for connecting a remote computer to the
corporate network, via e.g. a direct phone line or via the Internet.
Verification:
Also known as one-to-one or 1:1 comparison. The verification procedure
confirms whether the person in question is actually the person they
claim to be. The person’s current biometric data are compared only
with their own reference data. This authentication mode requires
another unique identifier such as a User ID, PIN, or smart card.
Verification is inherently faster and more secure than the
identification method.
Verification Algorithm
The algorithm used to check whether a user is who he says he is. Each
biometric device will have an associated verification algorithm.
WAN (Wide-Area-Network)
Similar to a LAN, but on a larger geographical scale.
W-LAN (Wireless LAN)
A wireless LAN is a wireless local area network that uses radio waves
as its carrier: where the network connections for end-users are
wireless. The main network structure usually uses cables.
Wiegand
Wiegand is the trade name for a technology used in card readers and
sensors, particularly for access control applications. Wiegand devices
were originally developed by HID Corporation.
A Wiegand card looks like a credit card. It works according to a
principle similar to that used in magnetic-stripe cards, such as those
used with bank automatic teller machines (ATMs). Instead of a band of
ferromagnetic material, the Wiegand card contains a set of embedded
wires. The wires are made of a special alloy with magnetic properties
that are difficult to duplicate.
Wiegand effect occurs over a wide range of temperatures. Therefore,
access control devices using this technology can function in hostile
environments. Other assets include rapid response time and
portability. These properties make Wiegand cards and readers ideal for
use in the field.
Wiegand cards
Wiegand cards are essentially magnetic field effect devices. As the
card is inserted or swiped through the reader an electromagnetic field
generated by the reader induces a voltage in the card causing it to
transmit its code. Unlike some insertion type systems, wiegand readers
are completely sealed against weather conditions and as a result have
a long live span. These cards are difficult to duplicate, highly
damage resistant, and offer a high level of security, but as with
proximity cards expensive, and generally can only be programmed by the
manufacturer.
Web server
A Web server is a program, which allows Web browsers to retrieve files
from computers connected to the Internet. The Web server listens for
requests from Web browsers and upon receiving a request for a file
sends it back to the browser.
The primary function of a Web server is to serve pages to other remote
computers; consequently, it needs to be installed on a computer that
is permanently connected to the Internet. It also controls access to
the server whilst monitoring and logging server access statistics.
WEP (Wired Equivalent Privacy)
A wireless security protocol, specified in the IEEE 802.11 standard,
which is designed to provide a wireless local area network (WLAN) with
a level of security and privacy comparable to that usually expected of
a wired LAN. Security is at two different levels; 40-bit and 128-bit
encryption. The higher the bit number, the more secure the encryption.
Web-based Biometrics
Web-based Biometrics is a simple, state of the art solution that
employees the web-based technology to identity, verify and
authenticate users.
The identification, verification or authentication can be done by
using fingerprint, face or a combination of both. Fingerprint
recognition requires a scanner to be installed on the client machine.
The face recognition software can work with a webcam, a regular camera
or an IP based camera
The user interface is a web-browser that everyone is familiar with and
comes installed with 99% of the OS. As soon a fingerprint reader and a
camera is installed on the client machine, it is ready to start
capturing the biometric information of the users and sending it to the
server for matching. This makes it virtually maintenance-free
client-side application and an ideal application for authenticating
users over the internet.
Benefits
• Being web based, the system offers the following advantages:
o Reduces IT Management costs.
o Simplifies deployment to clients.
o Reduces license costs while effectively increasing license
utilizations.
• Eliminates weak passwords as a vulnerability
• Password lifecycle management
o No need for password management - 40% of help desk calls are
password related (Gartner Group).
o No need for complicated passwords
o No password sharing
• Improves security of your organization
• Simplifies provisioning
• Robust audit trail
WINS (Windows Internet Naming Service)
Part of the Microsoft Windows NT Server, WINS manages the association
of workstation names and locations with IP addresses, without the user
or administrator having to be involved in each configuration change.
WPA-PSK (Wi-Fi Protected Access - Pre-Shared Key)
This wireless encryption method uses a pre-shared key (PSK) for key
management. Keys can usually be entered as manual hex values, as
hexadecimal characters, or as a Passphrase. WPA-PSK provides a greater
degree of security than WEP.